Insights from recent episode analysis
Audience Interest
Podcast Focus
Publishing Consistency
Platform Reach
Insights are generated by CastFox AI using publicly available data, episode content, and proprietary models.
Est. Listeners
Based on iTunes & Spotify (publisher stats).
- Per-Episode Audience
Est. listeners per new episode within ~30 days
10,001 - 25,000 - Monthly Reach
Unique listeners across all episodes (30 days)
25,001 - 75,000 - Active Followers
Loyal subscribers who consistently listen
5,001 - 15,000
Market Insights
Platform Distribution
Reach across major podcast platforms, updated hourly
Total Followers
—
Total Plays
—
Total Reviews
—
* Data sourced directly from platform APIs and aggregated hourly across all major podcast directories.
On the show
Recent episodes
Why Saving The World Destroys It
May 1, 2026
50m 42s
Why Forced Improvement Backfires
May 1, 2026
21m 18s
Cybersecurity Analytics - Module 12 - The Gap Between AI Accuracy & Truth
May 1, 2026
21m 15s
Cybersecurity Analytics - Module 11 - How Behavioral Analytics Catches Insider Threats
May 1, 2026
21m 51s
Cybersecurity Analytics - Module 10 - Why Perfect Security Is Mathematically Impossible
May 1, 2026
18m 45s
Social Links & Contact
Official channels & resources
Official Website
Login
RSS Feed
Login
| Date | Episode | Description | Length | ||||||
|---|---|---|---|---|---|---|---|---|---|
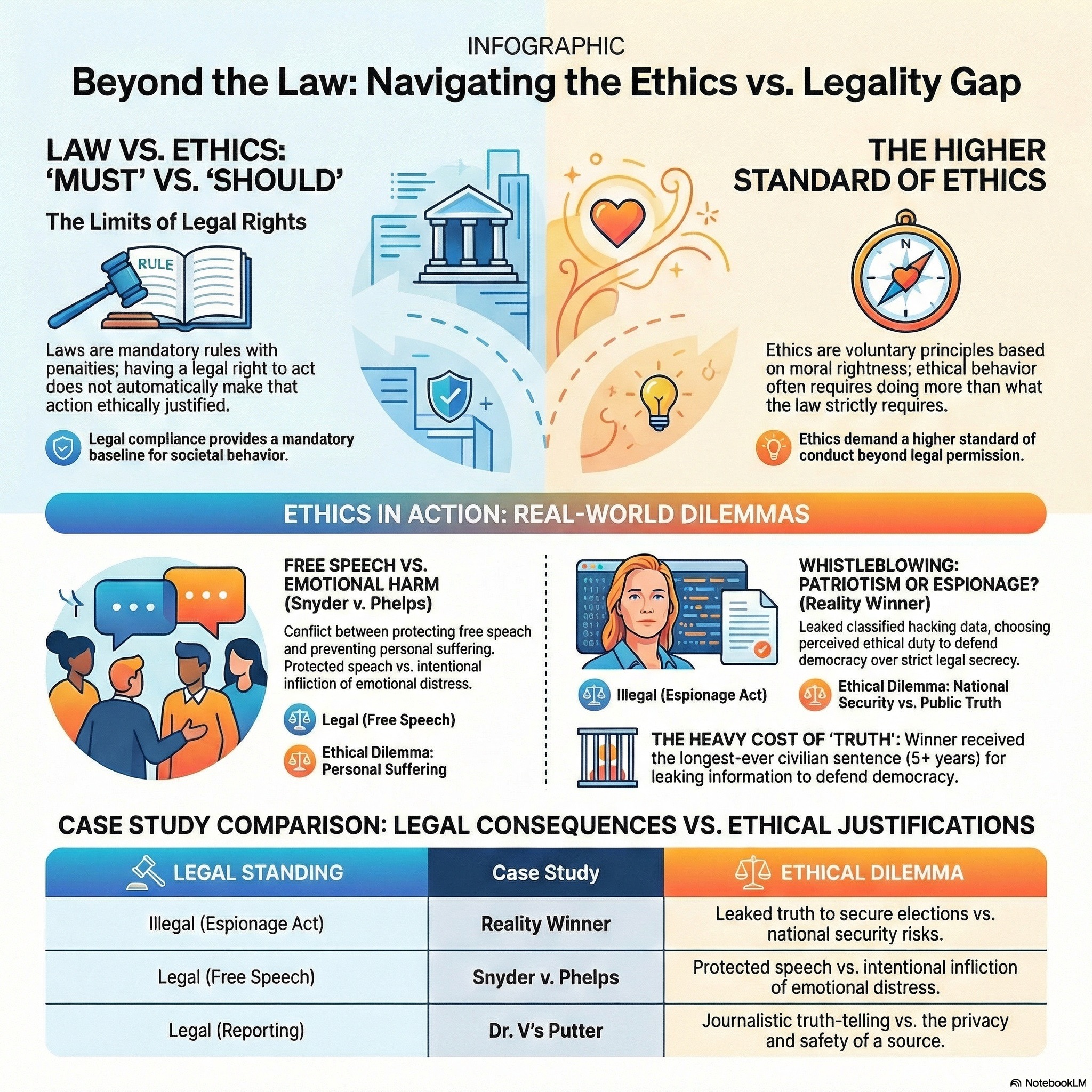
| 5/1/26 | 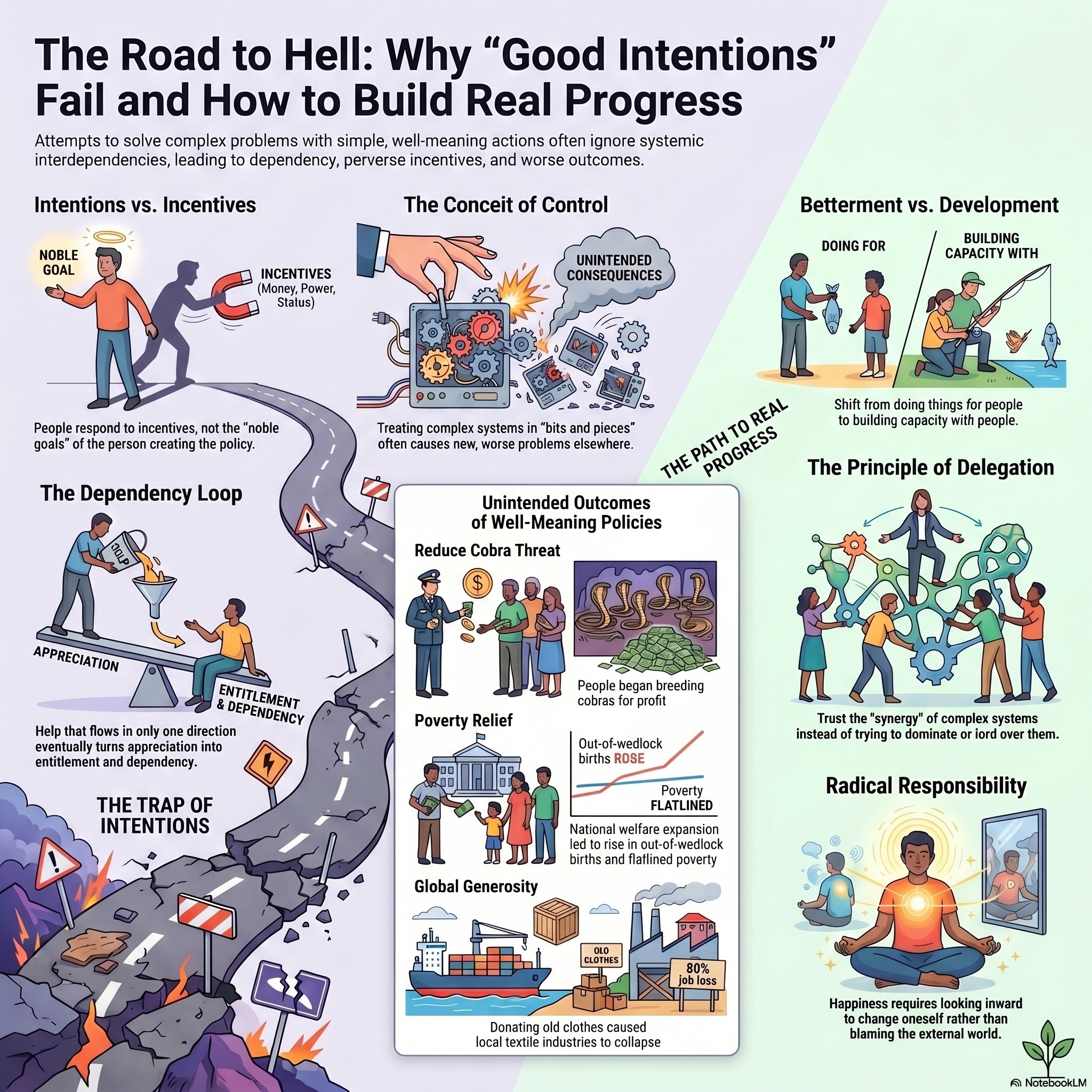 Why Saving The World Destroys It Why Saving The World Destroys It | This podcast explores the paradox of good intentions, suggesting that efforts to improve the world or oneself often backfire when they lack genuine awareness or trust. Philosophically, the texts argue that nature and life are inherently purposeless, and forcing a rigid moral or practical goal onto them can lead to destructive dependency and unintended consequences. Economically and socially, the material highlights how misaligned incentives and charitable interventions frequently undermine local systems, creating cycles of poverty and inefficiencyrather than true development. Additionally, the sources critique the illusion of the ego and the victim mindset, noting that individual growth requires a sincere confrontation with reality rather than seeking external validation. Ultimately, the collection advocates for living in the present moment and relinquishing the urge to control complex systems. Through diverse examples like hyperinflation and toxic charity, the text warns that a conceited desire to do good may inadvertently pave a road to disaster. | 50m 42s | ||||||
| 5/1/26 | 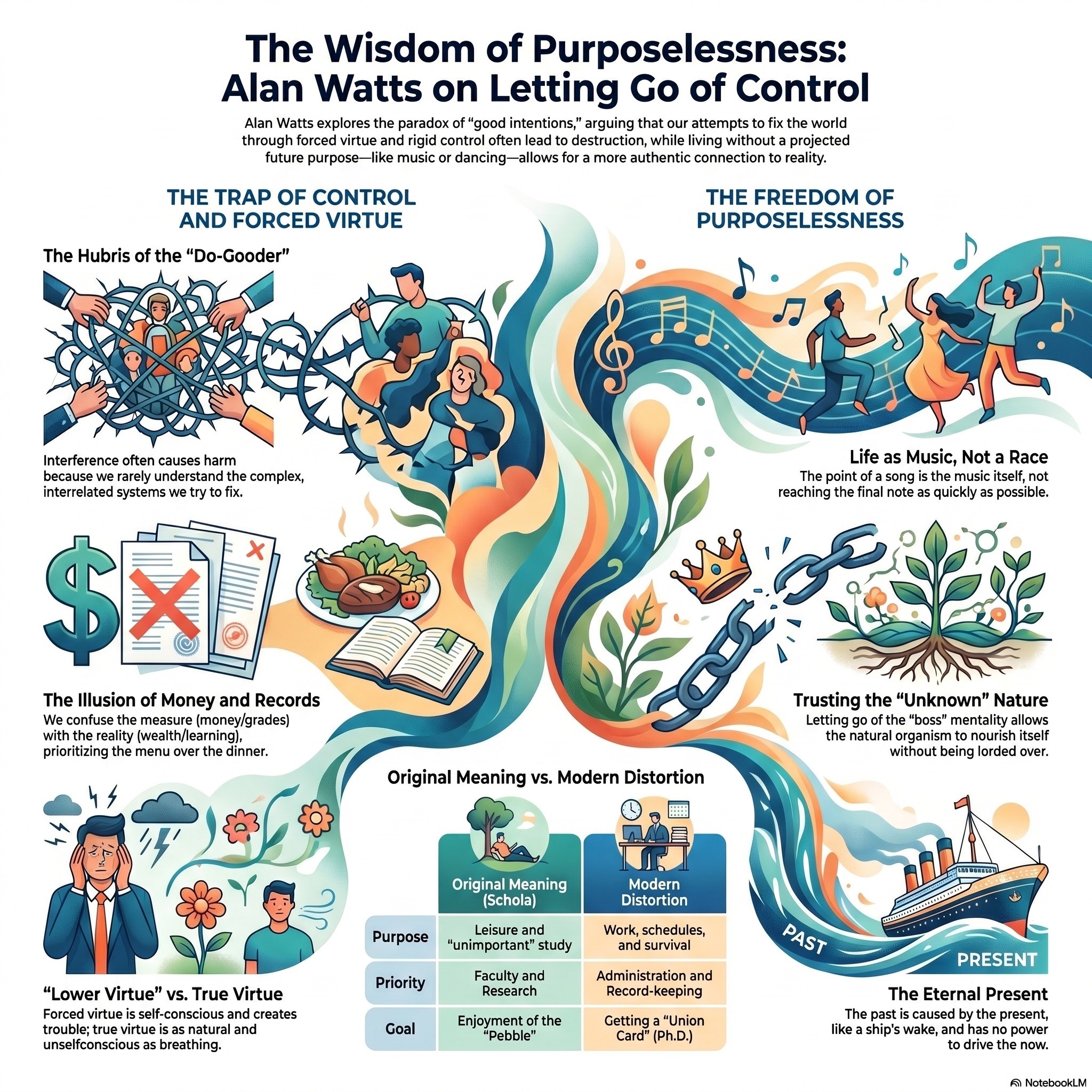 Why Forced Improvement Backfires Why Forced Improvement Backfires | This podcast examines how misguided altruism and rigid social systems often produce harmful, unintended outcomes. Using the philosophy of Alan Watts and modern economic examples, the texts argue that enforced virtue and government intervention frequently backfire because they prioritize outward control over an organic trust in nature. This dynamic is illustrated through toxic charity that creates dependency, inflationary policies that destroy wealth, and an education system that favors bureaucracy over genuine learning. The narratives suggest that true improvement comes from personal accountability and a "purposeless" appreciation of the present rather than the conceit of trying to "fix" others. Ultimately, the collection warns that a preoccupation with righteousness can lead to a cycle of failure and psychological stagnation. | 21m 18s | ||||||
| 5/1/26 | 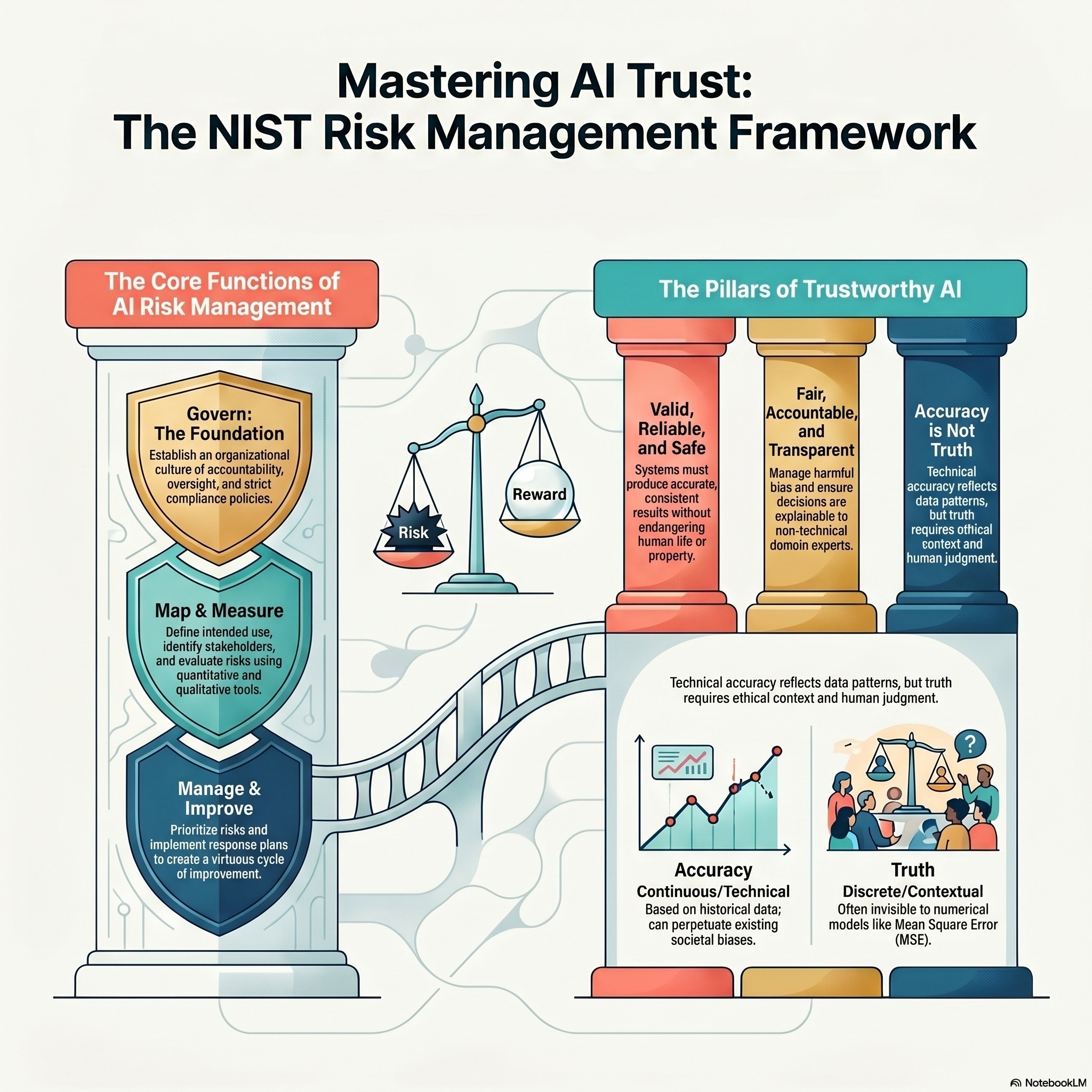 Cybersecurity Analytics - Module 12 - The Gap Between AI Accuracy & Truth Cybersecurity Analytics - Module 12 - The Gap Between AI Accuracy & Truth | This podcast outlines the core components of the NIST AI Risk Management Framework, focusing on the essential functions of governance, mapping, measurement, and management. To ensure responsible AI deployment, the framework highlights the importance of establishing clear policies, identifying stakeholder interests, and evaluating performance metrics like fairness and robustness. It emphasizes organizational accountability through oversight structures and systematic risk response planning during the technology's lifecycle. Additionally, the text defines the characteristics of trustworthy AI, which include safety, security, and the active mitigation of harmful biases. By integrating these functions, organizations can maintain transparency and ensure their systems remain valid and reliable. | 21m 15s | ||||||
| 5/1/26 | 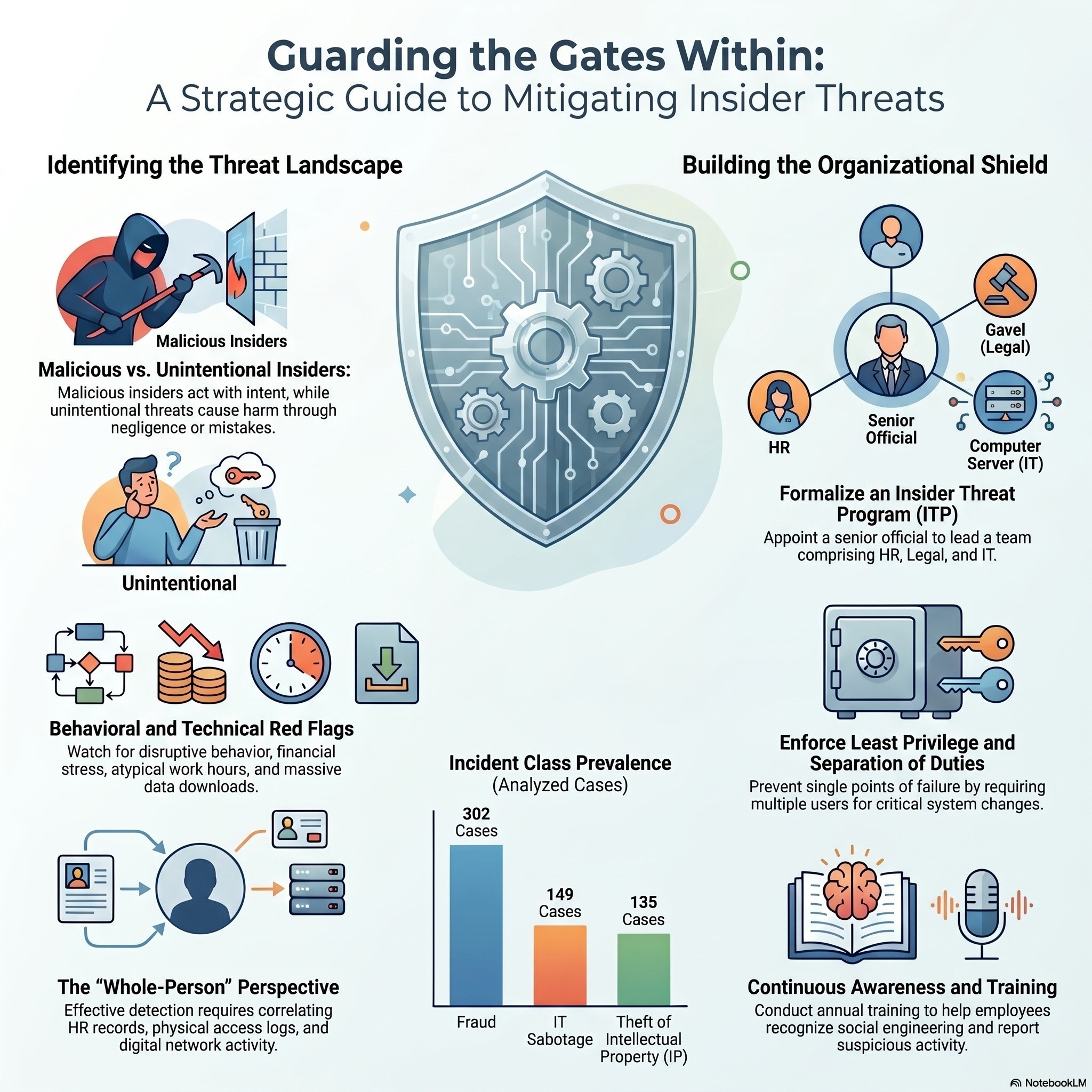 Cybersecurity Analytics - Module 11 - How Behavioral Analytics Catches Insider Threats Cybersecurity Analytics - Module 11 - How Behavioral Analytics Catches Insider Threats | This podcast details the use of User and Entity Behavior Analytics (UEBA) to identify and mitigate insider threats within a digital environment. By establishing behavioral baselines for login times, file access, and network norms, organizations can detect anomalies such as sudden data hoarding or impossible travel. The system aggregates various data sources, including authentication logs and cloud activity, to flag deviations that suggest misuse of legitimate access. It illustrates how these risk scores trigger formal investigations and responses. Ultimately, the source emphasizes that while automated profiling is powerful, effective security still requires human oversight and a commitment to user privacy. | 21m 51s | ||||||
| 5/1/26 | 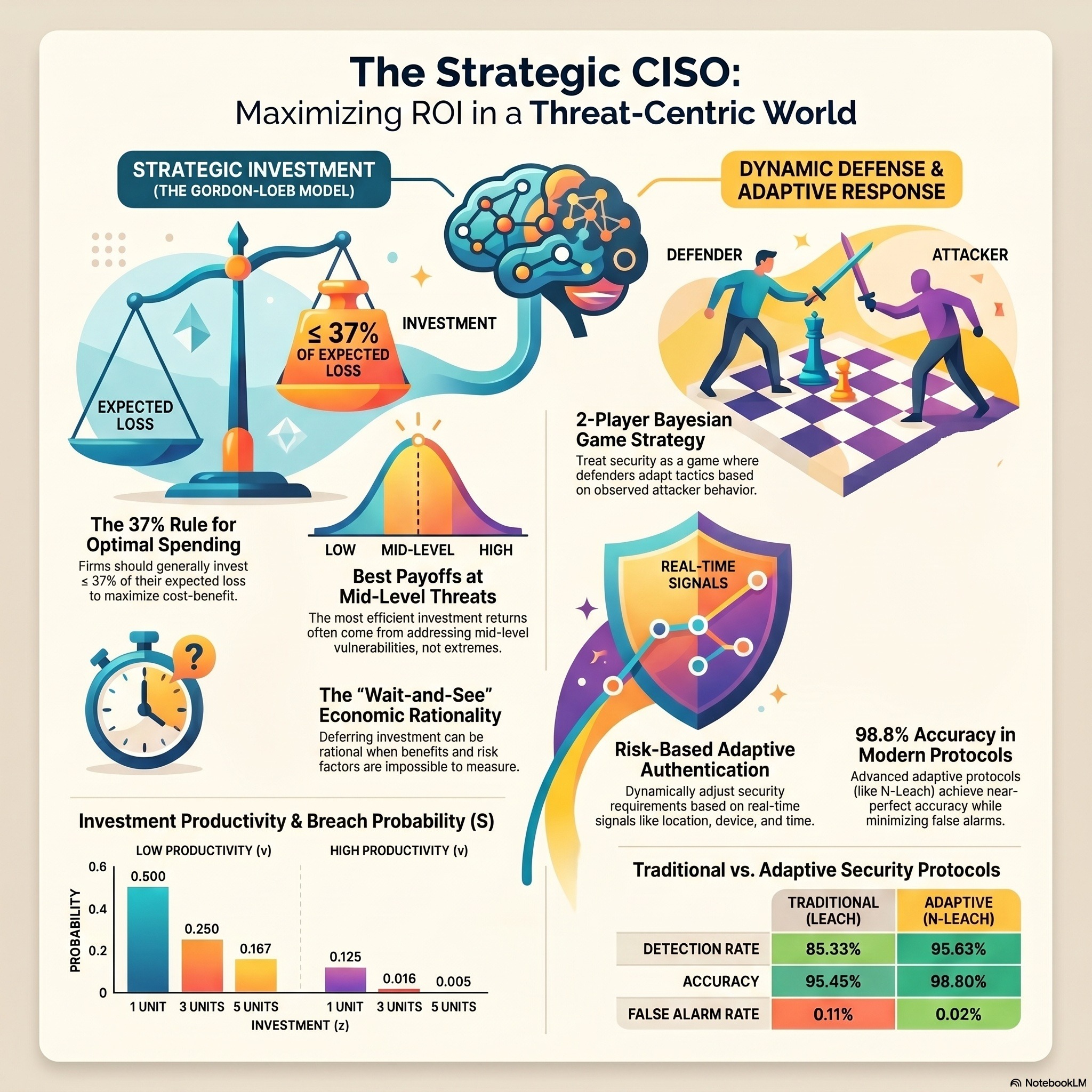 Cybersecurity Analytics - Module 10 - Why Perfect Security Is Mathematically Impossible Cybersecurity Analytics - Module 10 - Why Perfect Security Is Mathematically Impossible | This podcast examines cybersecurity from both an economic and technological standpoint, focusing on how organizations can efficiently manage digital risks. One source introduces the Gordon-Loeb Model, which uses mathematical frameworks to help executives determine the optimal level of investment by balancing potential losses against the productivity of security spending. This model suggests that firms should generally invest no more than 37% of their expected losses from a breach to ensure cost-effectiveness. Complementing this financial view, the second source explains adaptive authentication, a dynamic security method that adjusts access requirements based on real-time risk signals like user behavior and location. Together, these texts emphasize that 100% security is impossible, requiring leaders to make strategic, data-driven decisions that balance robust protection with operational efficiency. Organizations must prioritize their most valuable assets and use context-aware tools to mitigate threats while minimizing friction for legitimate users. | 18m 45s | ||||||
| 5/1/26 | 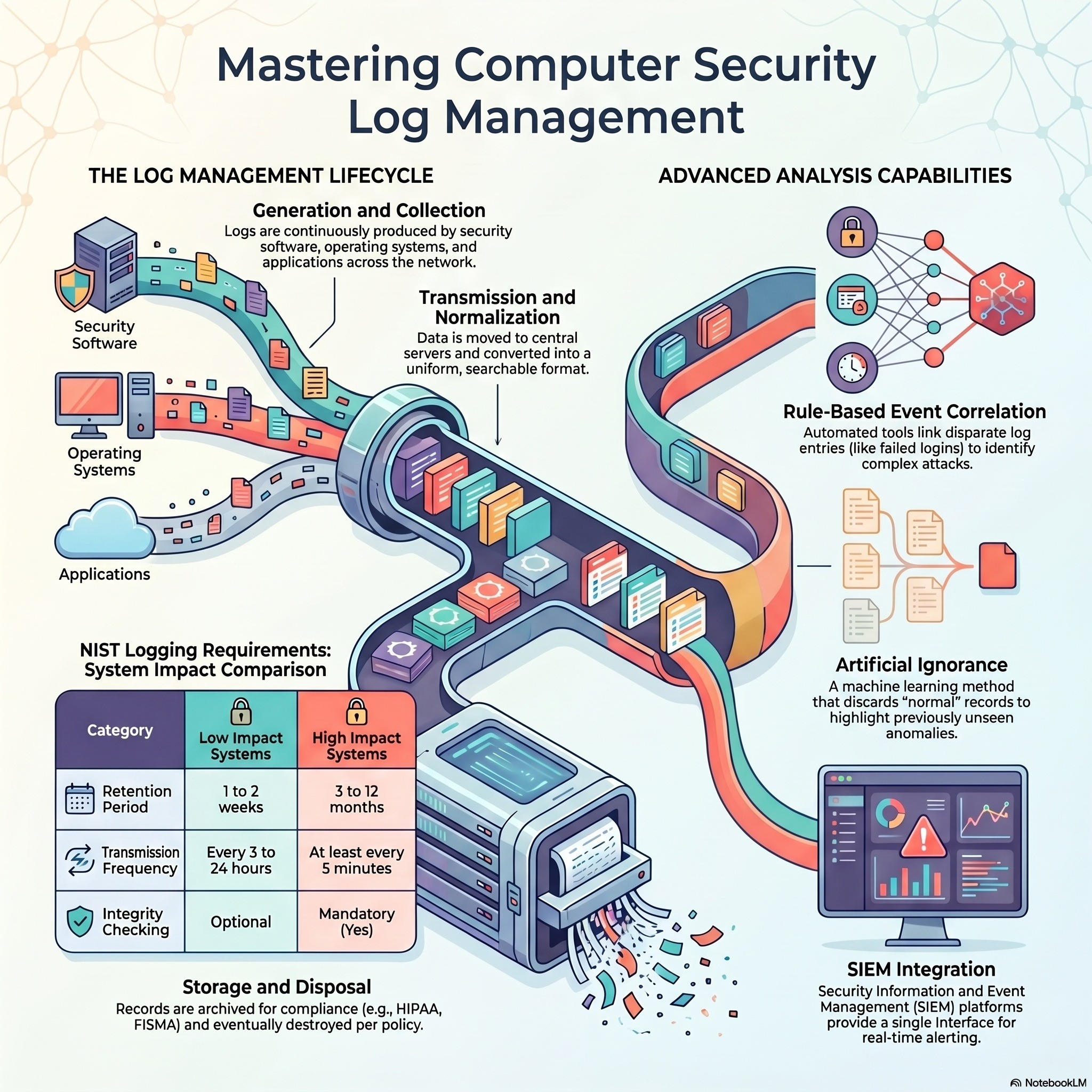 Cybersecurity Analytics - Module 09 - Taming The Security Data Hurricane Cybersecurity Analytics - Module 09 - Taming The Security Data Hurricane | This podcast explains how data engineering serves as the vital foundation for converting messy, disorganized security logs into actionable intelligence. Because machine learning models require high-quality inputs, the source outlines a log ingestion pipeline that focuses on parsing, normalization, and feature extraction to ensure accurate analysis. It compares the roles of SIEMs and data lakes, highlighting the balance between real-time streaming for immediate detection and batch processing for historical threat hunting. The podcast also addresses the operational hurdles of managing large-scale telemetry, such as storage costs and data quality issues like missing fields or timing errors. Ultimately, the material emphasizes that while automated pipelines drive modern security analytics, human expertise remains essential for designing schemas and interpreting complex anomalies. Use examples, clarify terms, and ensure understanding. | 24m 46s | ||||||
| 5/1/26 | 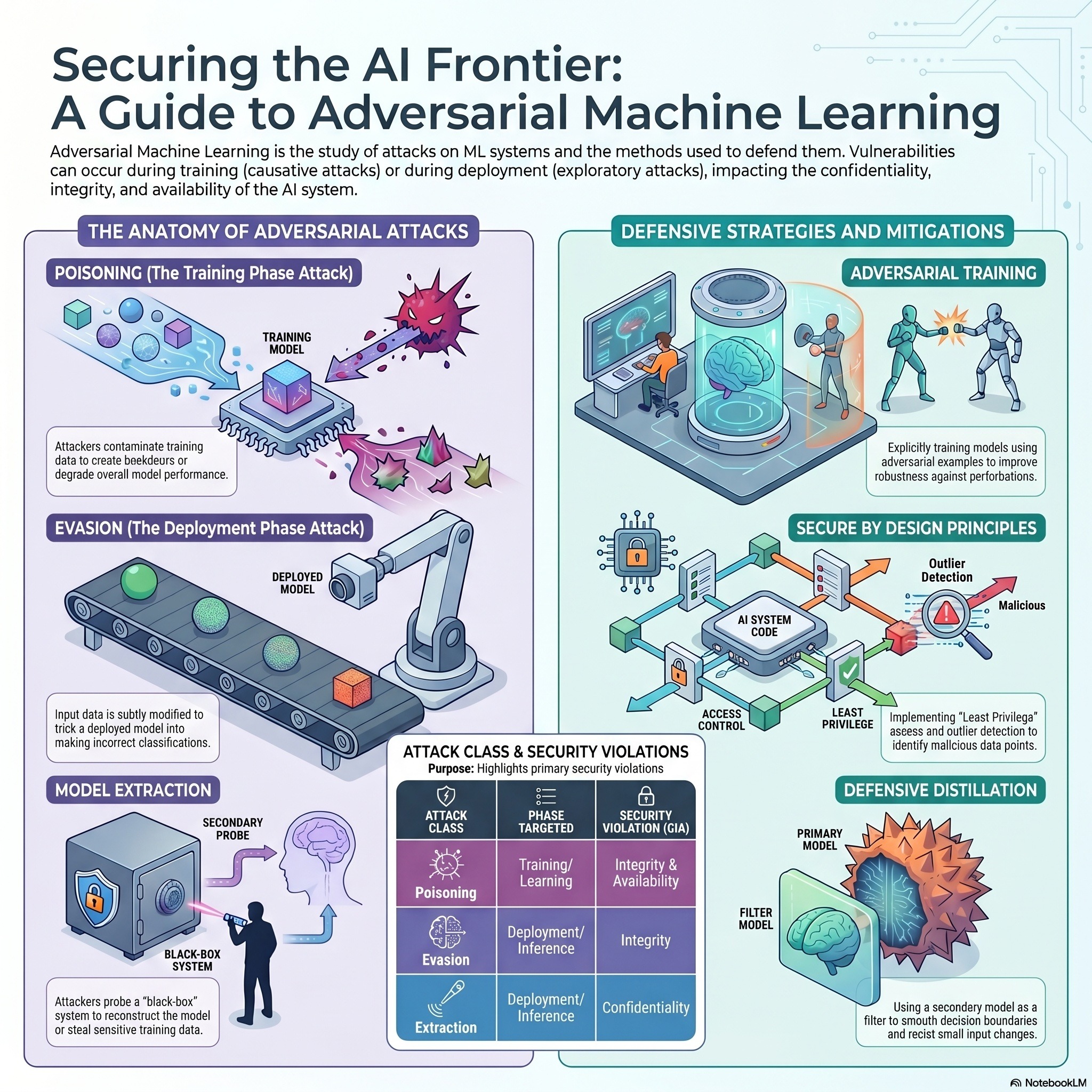 Cybersecurity Analytics - Module 08 - Tricking AI With Invisible Noise Cybersecurity Analytics - Module 08 - Tricking AI With Invisible Noise | This podcast examines the foundational concepts of adversarial machine learning, focusing on how vulnerabilities emerge from imperfect learning and blind spots within a model’s logic. Exploratory attacks exploit these weaknesses after a system is deployed, requiring no direct access to the original training data to cause errors. These threats are categorized by their specificity, ranging from targeted attacks that subtly redirect a prediction to indiscriminate attacks that aim for total system failure. The material also highlights the adversarial space, which contains exploitable regions that exist because a model's abstraction of reality is inherently limited. Finally, the text explains that while a theoretical minimum error exists in classical settings, attackers in adversarial environments can actively increase this rate. This dynamic demonstrates that simply increasing the volume of data or the complexity of a model does not guarantee perfect security. | 20m 20s | ||||||
| 5/1/26 | 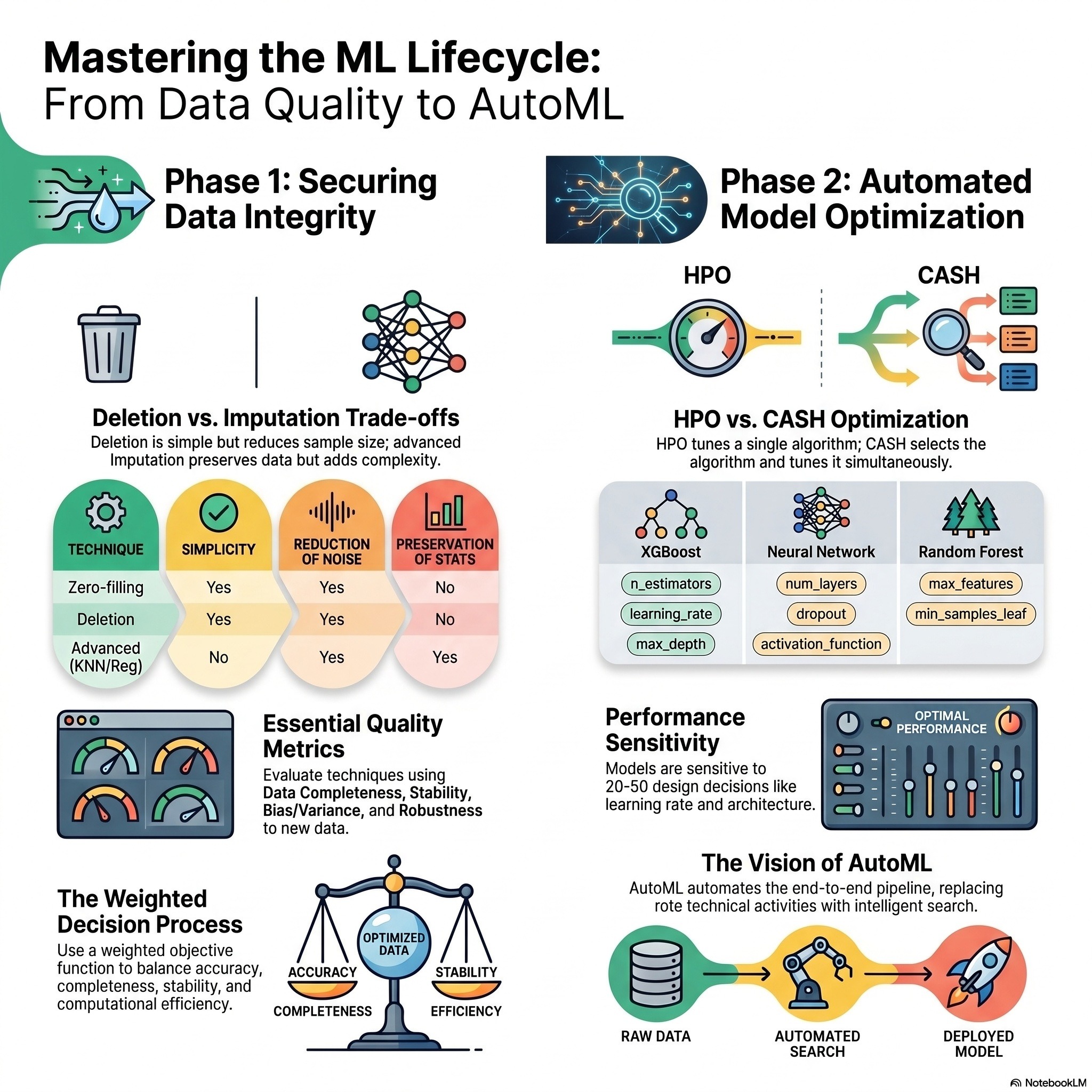 Cybersecurity Analytics - Module 07 - Why Machine Learning Models Degrade In Production Cybersecurity Analytics - Module 07 - Why Machine Learning Models Degrade In Production | This podcast outlines critical strategies for maintaining high-quality machine learning (ML) lifecycles, with a specific focus on feedback loops and data integrity. One source details the AWS Well-Architected Framework, which promotes systematic monitoring and automated retraining to combat model performance degradation over time. Another emphasizes that the presence of missing data is a primary challenge, requiring a rigorous evaluation of imputation techniques like mean substitution or regression to preserve accuracy. Collectively, the texts advocate for a structured evaluation framework that considers factors such as computational efficiency, stability, and bias reduction. By integrating these MLOps best practices, organizations can foster a culture of continuous experimentation and improve the reliability of predictive models. | 20m 24s | ||||||
| 5/1/26 | 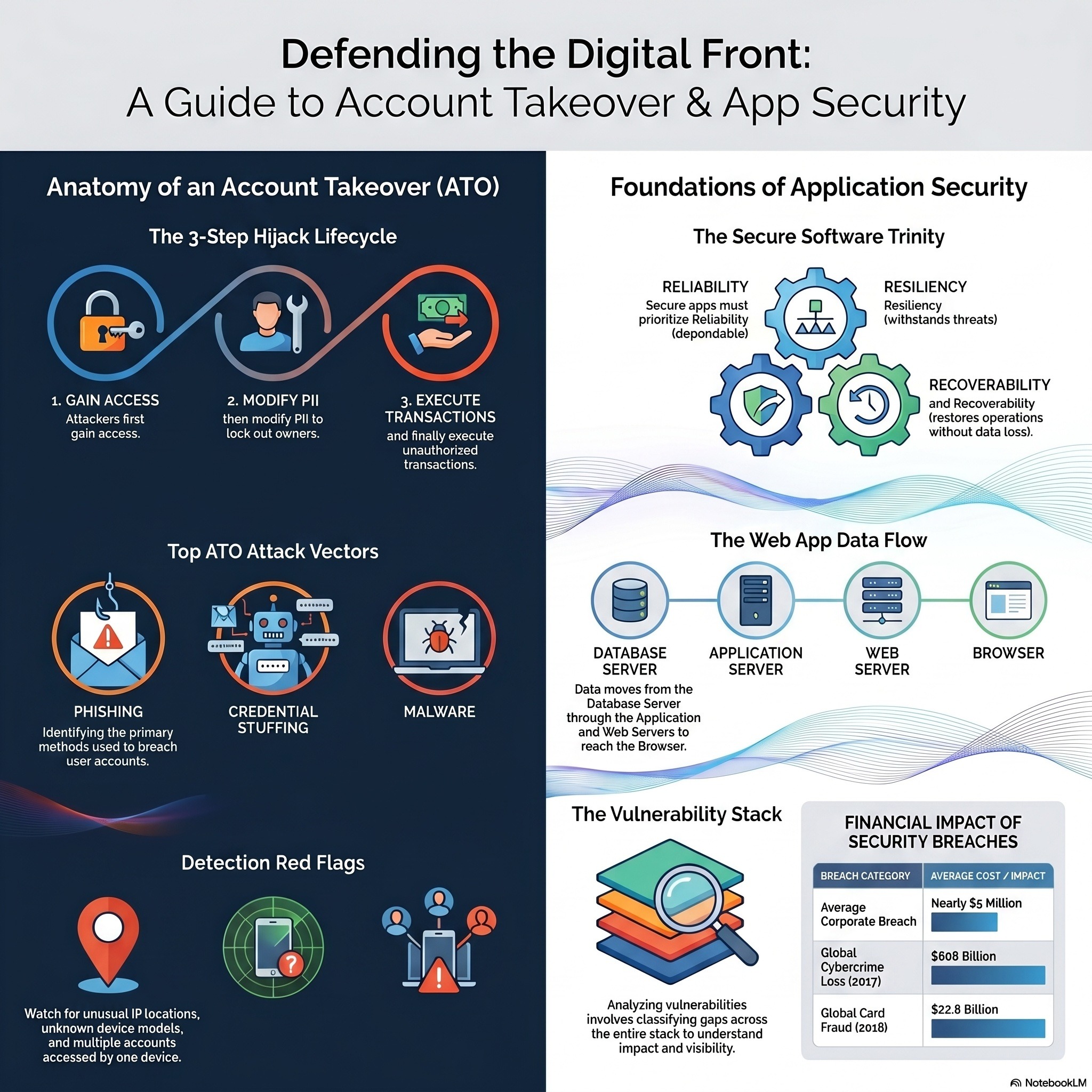 Cybersecurity Analytics - Module 06 - Stopping Account Takeovers In A Glass Vault Cybersecurity Analytics - Module 06 - Stopping Account Takeovers In A Glass Vault | This podcast offers a comprehensive look at the economic impact, technical mechanisms, and prevention strategies associated with modern digital fraud, specifically focusing on account takeover (ATO) and payment systems. The texts detail how criminals exploit vulnerabilities in credit cards, mobile payments, and telecommunications through methods like phishing, credential stuffing, and hardware skimming. While businesses face significant financial and reputational risks from these breaches, individuals are also targeted via social engineering and sophisticated malware. To combat these threats, the authors recommend multi-layered security approaches, including biometric verification, behavioral analytics, and multi-factor authentication. Ultimately, the sources emphasize that as cybercriminals evolve through automation and AI, service providers must adopt real-time detection solutions to safeguard consumer data and financial assets. | 21m 50s | ||||||
| 4/29/26 | 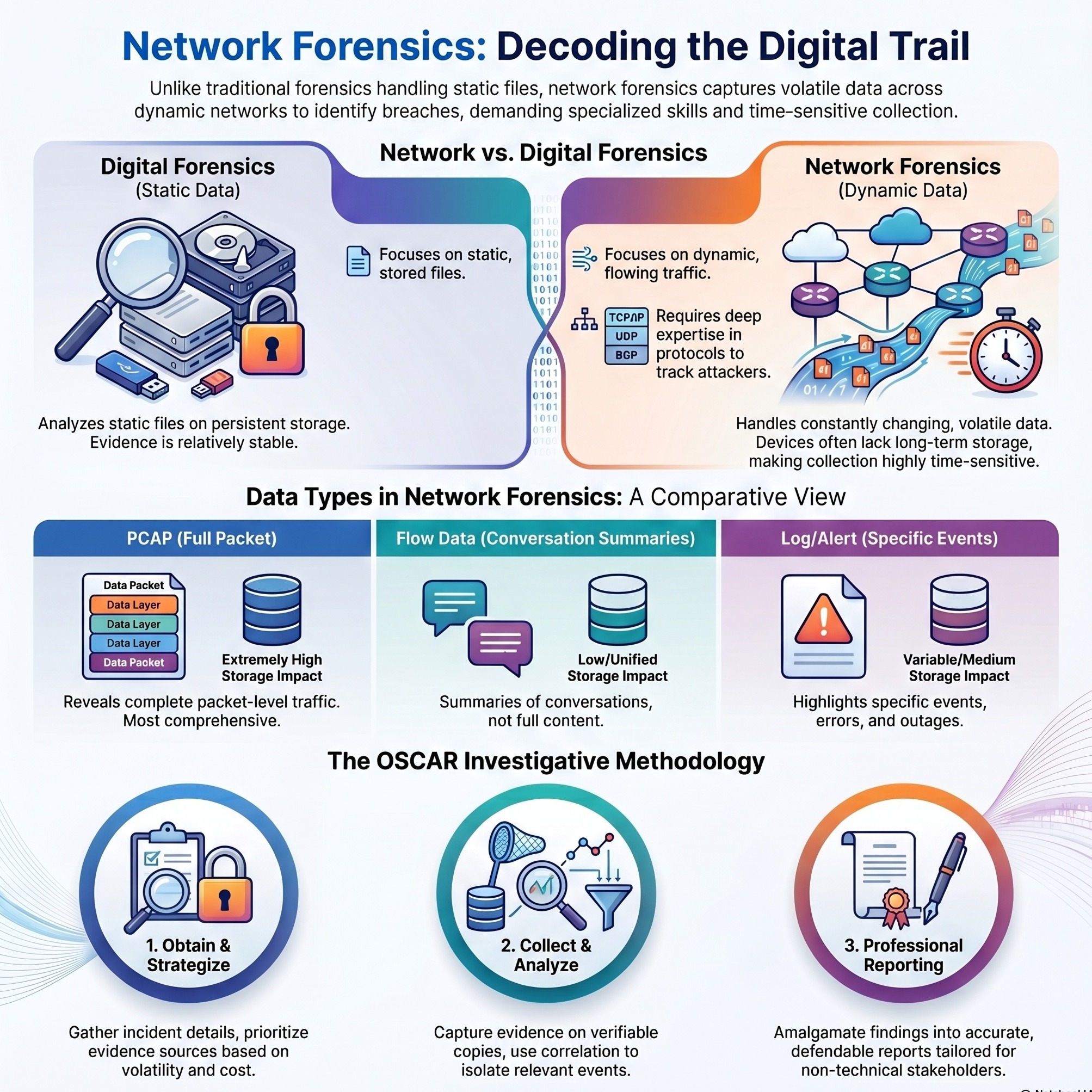 Cybersecurity Analytics - Module 05 - Hunting Cyber Threats In Encrypted Traffic Cybersecurity Analytics - Module 05 - Hunting Cyber Threats In Encrypted Traffic | This podcast provides a comprehensive network traffic data analysis using real-world traces. The research utilizes various open-source tools like tcpdump, tcptrace, and CoralReef alongside Matlab to examine traffic at the packet, flow, and connection levels. Key areas of investigation include protocol distribution, packet lengths, TCP retransmissions, and round-trip times. The author identifies significant patterns, such as the heavy-tailed nature of flow sizes and the prevalence of Zipf-type distributions in network traffic. Ultimately, the podcast described framework for network analysts to improve traffic engineering and resource optimization. | 20m 14s | ||||||
Want analysis for the episodes below?Free for Pro Submit a request, we'll have your selected episodes analyzed within an hour. Free, at no cost to you, for Pro users. | |||||||||
| 4/28/26 | 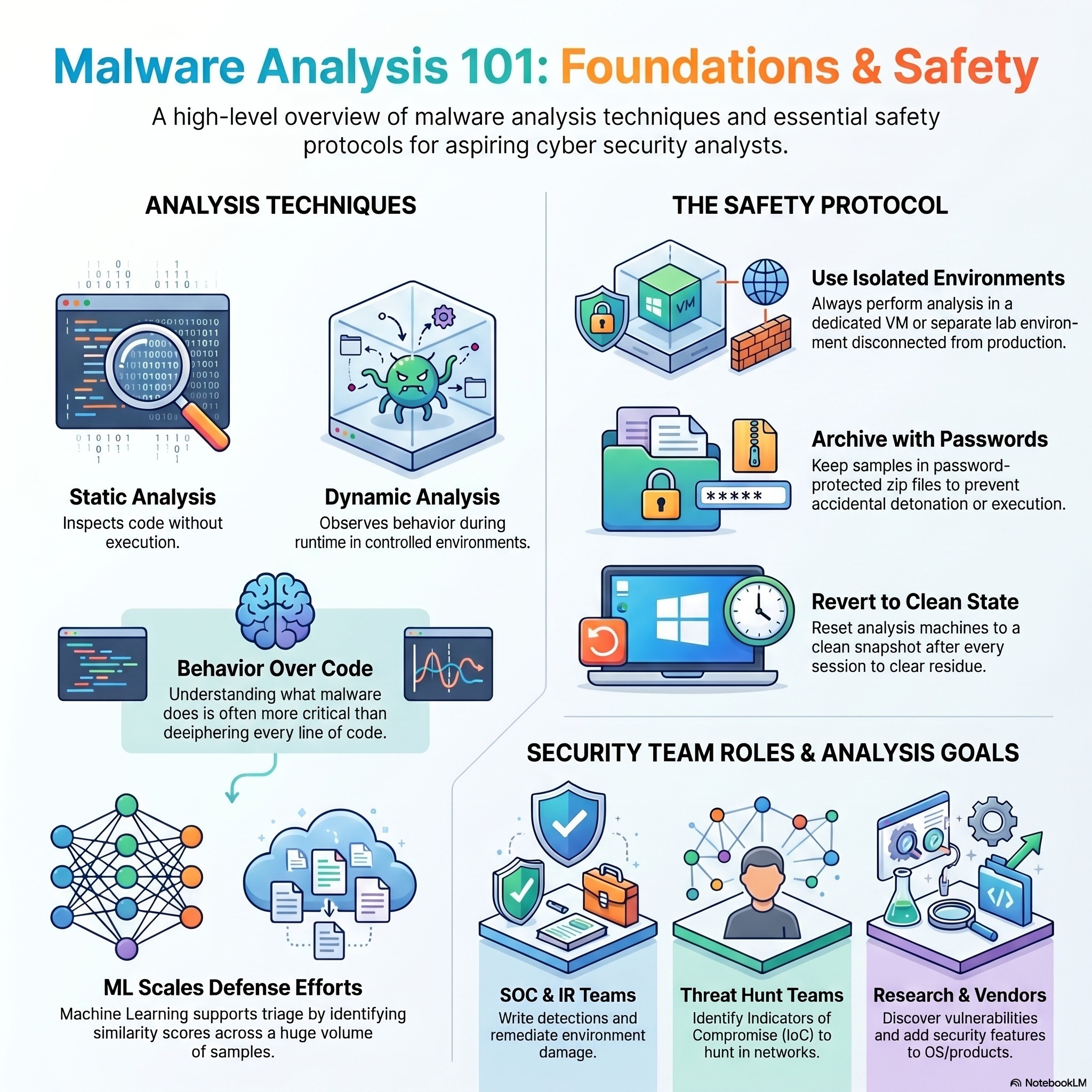 Cybersecurity Analytics - Module 04 - Malware Analysis From Assembly To AI Cybersecurity Analytics - Module 04 - Malware Analysis From Assembly To AI | This podcast provides a comprehensive overview of malware analysis and reverse engineering, moving from foundational theory to advanced defensive technologies. It categorizes malicious software into types like droppers, info-stealers, and fileless variants, while outlining a standard attack lifecycle that includes reconnaissance and privilege escalation. To safely study these threats, the materials emphasize operational security through the use of isolated virtual machines and sandboxes. The texts further distinguish between static analysis, which examines a file's blueprints, and dynamic analysis, which monitors the code's behavior during execution. Because modern threats use obfuscation and evasion to bypass human inspection, the sources highlight the necessity of machine learning and adversarial training to automate defenses. Finally, the collection offers practical study plans and academic resources for students looking to master the complex assembly language skills required to dismantle sophisticated cyber weapons. | 19m 04s | ||||||
| 4/28/26 | 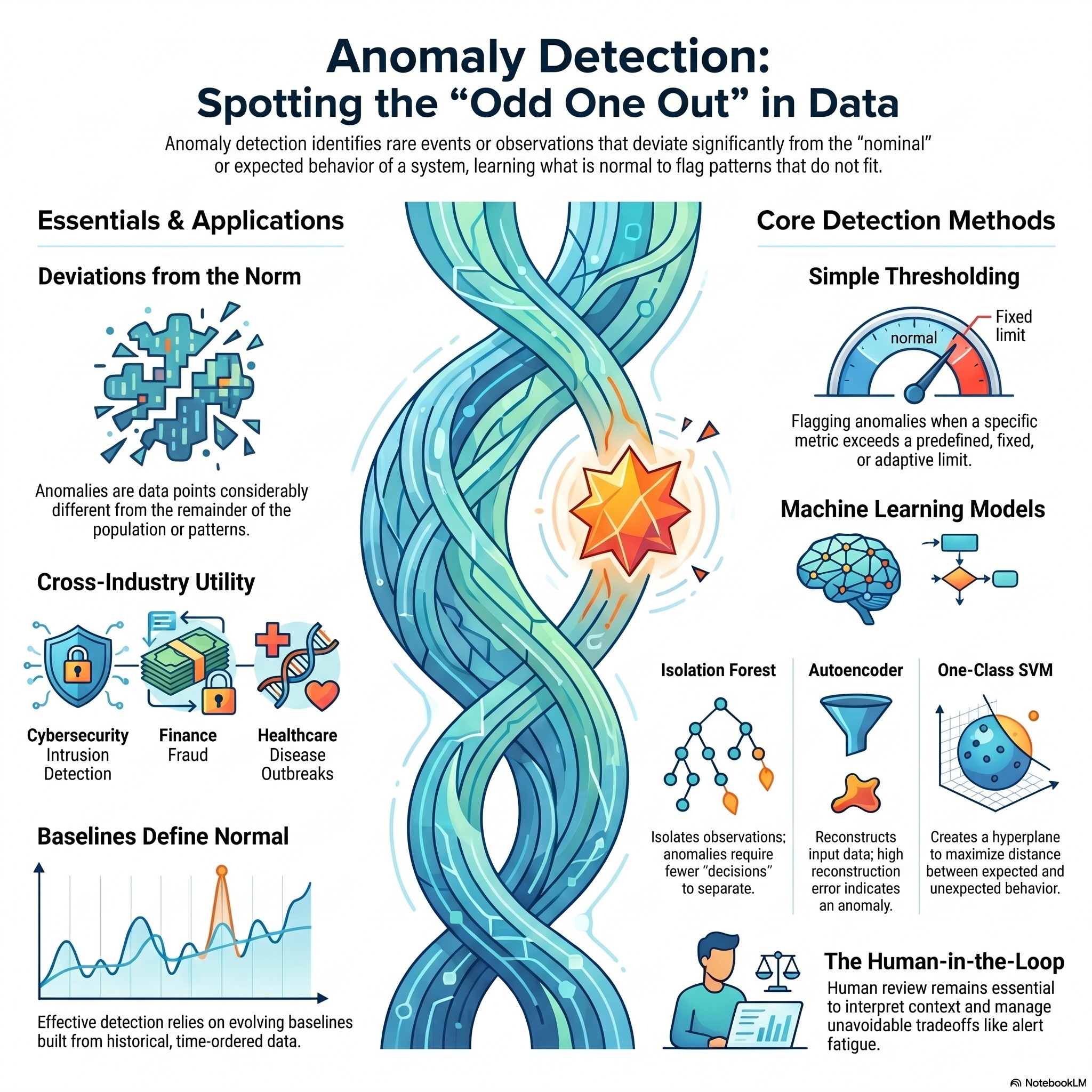 Cybersecurity Analytics - Module 03 - How Machines Find Anomalies Without Labels Cybersecurity Analytics - Module 03 - How Machines Find Anomalies Without Labels | Anomaly detection is the process of identifying data points or behaviors that deviate significantly from established normal patterns. This podcast explains that while anomalies are not always faults, they serve as vital indicators for fraud detection, cybersecurity, and predictive maintenance. Various methodologies are employed to flag these irregularities, ranging from simple thresholds to advanced machine learning models like auto encoders and isolation forests. By training algorithms on nominal data, systems can learn to recognize the "standard" state and alert operators to subtle, high-risk changes. Despite the power of automated detection, the literature emphasizes that human oversight remains essential to interpret context and manage false positives. Ultimately, these techniques provide an early warning system across diverse industries by highlighting the "odd one out" in complex datasets. | 21m 35s | ||||||
| 4/25/26 | 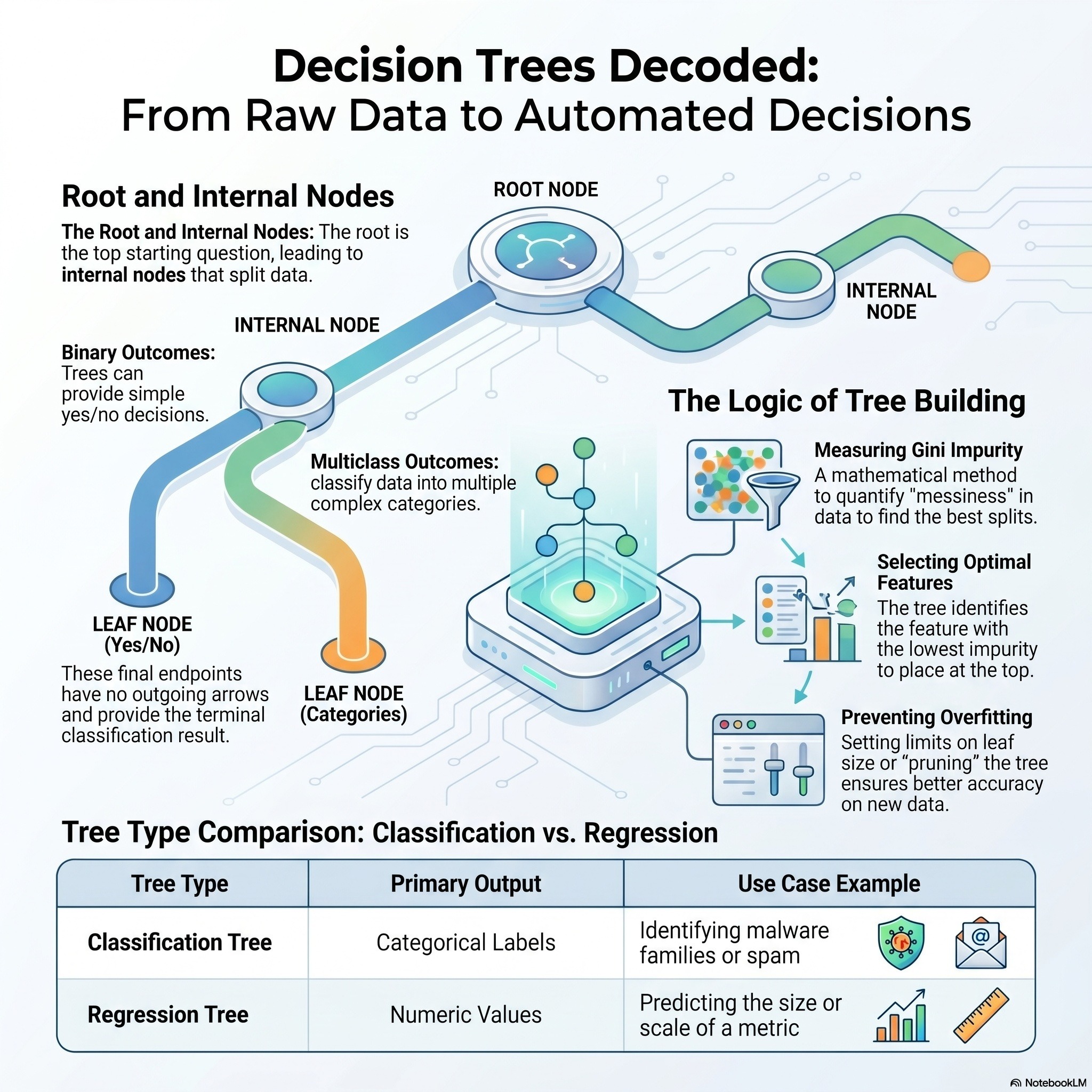 Cybersecurity Analytics - Module 02 - The Difference Between Classification & Clustering Cybersecurity Analytics - Module 02 - The Difference Between Classification & Clustering | Machine learning operates by identifying trends in past information to forecast future events, though these results are based on likelihoods rather than certainties. These systems address various challenges, including classification, regression, clustering, and anomaly detection, with each method designed to answer specific types of questions. For example, classification is a vital tool in cybersecurity that organizes data into established groups based on previously identified examples. While these automated processes are powerful, they are fundamentally imperfect, making the inclusion of human oversight necessary to manage errors. Ultimately, the quality of features used in a model often carries more significance than the specific mathematical formulas applied. These sources emphasize that while technology can automate complex tasks, people remain essential to the overall process. | 19m 37s | ||||||
| 4/25/26 | 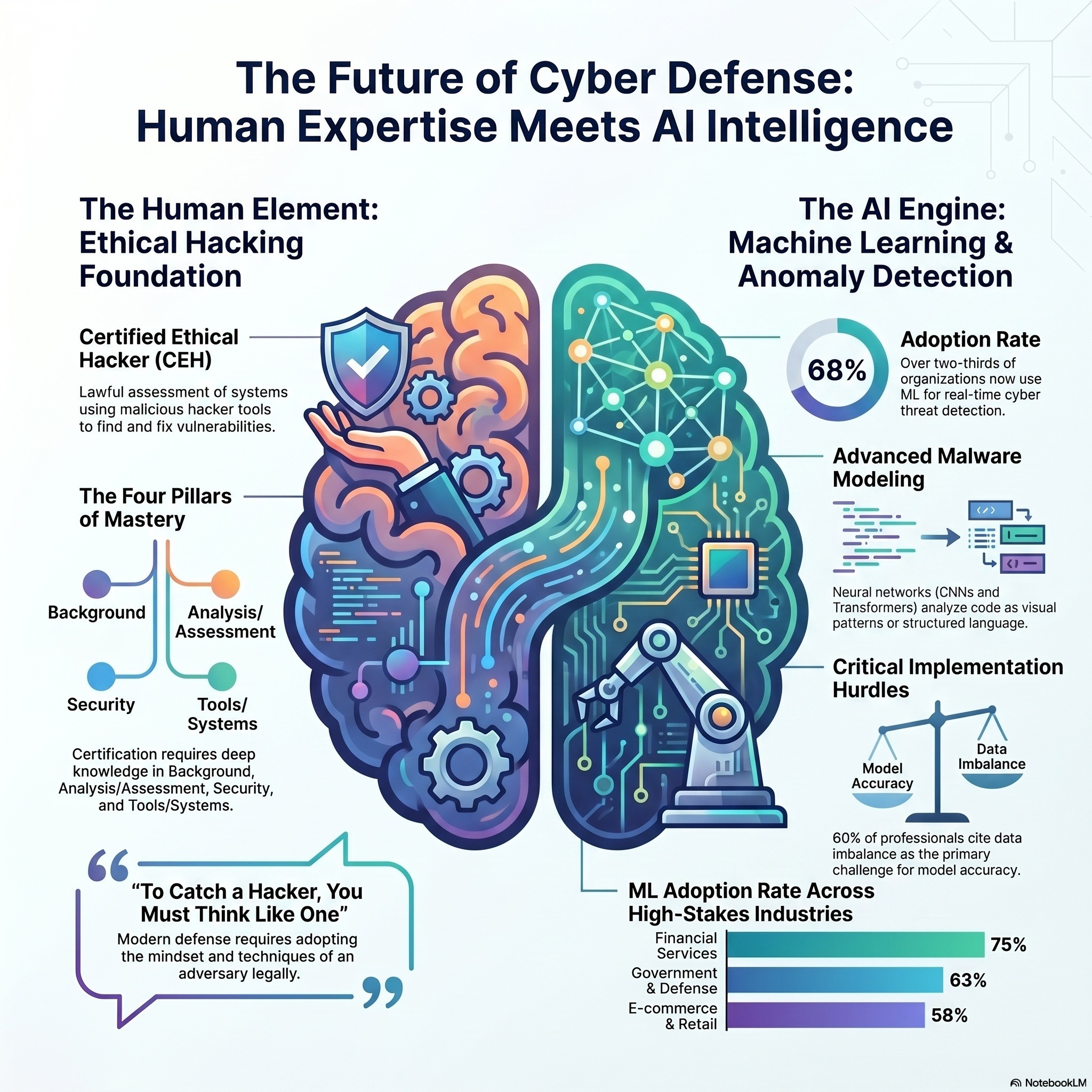 Cybersecurity Analytics - Module 01 - The Machine Learning Arms Race In Cybersecurity Cybersecurity Analytics - Module 01 - The Machine Learning Arms Race In Cybersecurity | The provided podcast serves as the official Candidate Handbook for the Certified Ethical Hacker (C|EH) credential, issued by the EC-Council. It establishes the eligibility requirements for applicants, including mandated professional experience or the completion of authorized training programs. The document details the exam structure, which consists of 125 questions over a four-hour duration, and outlines strict retake and renewal policies. Furthermore, the handbook emphasizes a rigorous Code of Ethics and Non-Disclosure Agreements designed to protect the integrity of the certification. Candidates are also provided with information on logo usage guidelines, appeal processes, and the continuing education credits required to maintain active status. Overall, this source functions as a comprehensive manual for professionals seeking to validate their skills in vulnerability assessment and network security. | 22m 27s | ||||||
| 3/25/26 | 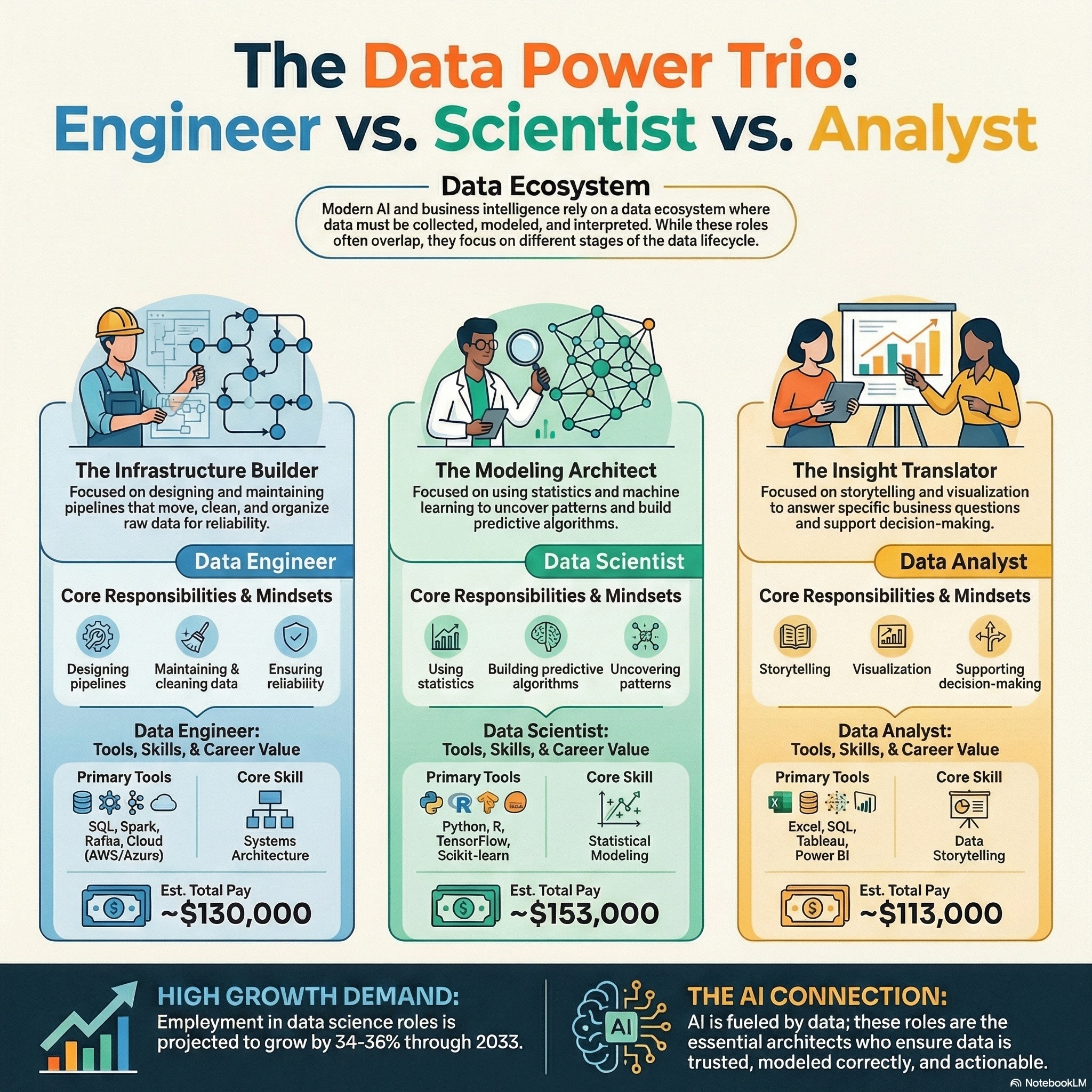 Data Engineer, Data Scientist, Data Analyst - What Do They Do? Data Engineer, Data Scientist, Data Analyst - What Do They Do? | This podcast provides a comprehensive comparison between the professional roles of data engineers and data scientists, highlighting their unique contributions to the modern tech landscape. While data engineers focus on the foundational aspects of building, maintaining, and scaling the infrastructure used to move and clean raw information, data scientists specialize in performing statistical analysis and creating predictive models to uncover strategic insights. The documentation outlines the specific technical toolkits for each path, noting that engineers prioritize systems like SQL and Spark, whereas scientists frequently utilize Python and machine learning frameworks. Additionally, the texts explore educational backgrounds, salary expectations, and projected job market growth, illustrating how these two positions function as interdependent components of a single data pipeline. By examining the different mindsets required for each career, the sources serve as a guide for individuals determining which specialty aligns best with their personal strengths and professional goals. | 13m 19s | ||||||
| 3/6/26 | 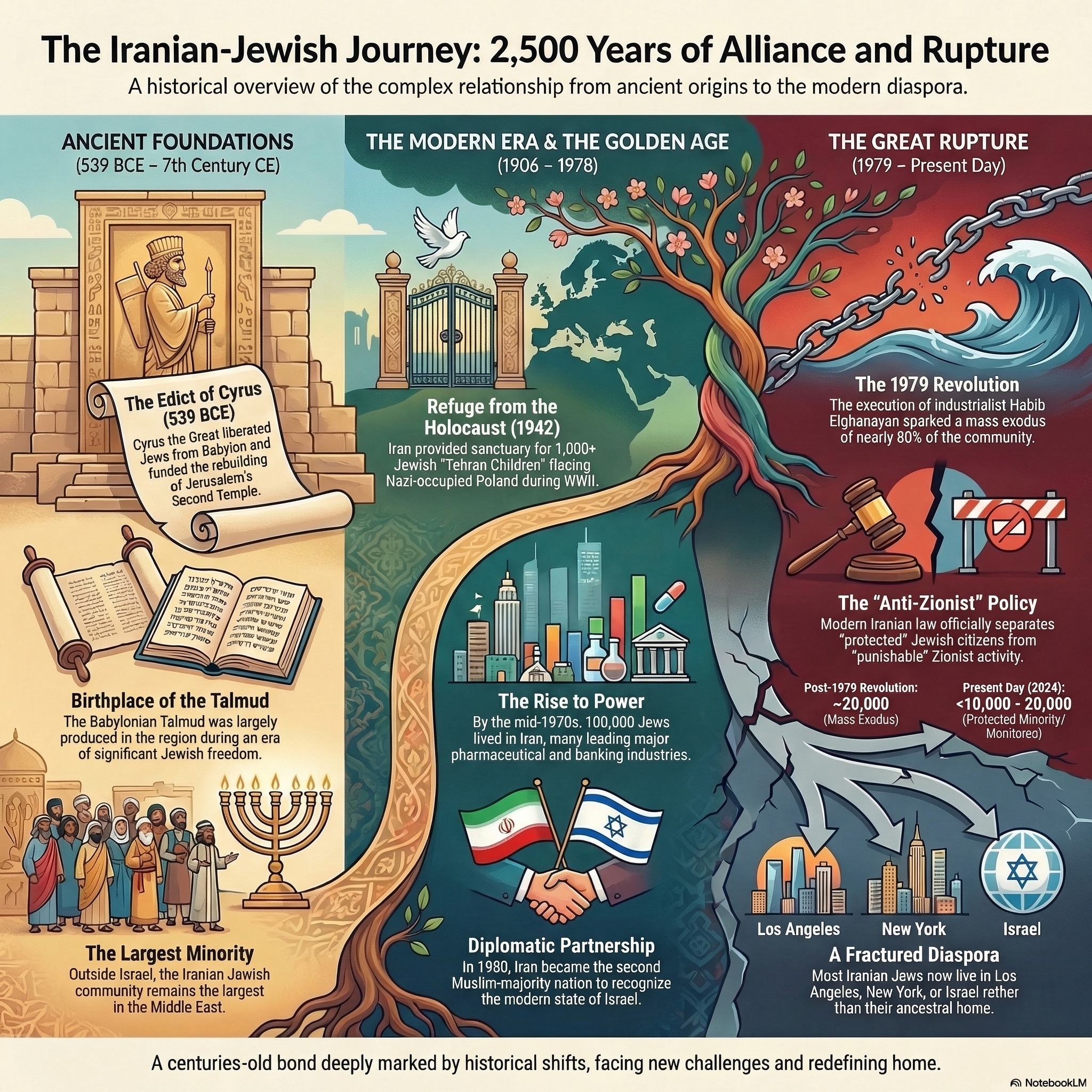 The Persians & The Jewish People The Persians & The Jewish People | This podcast examines the 2,700-year history of the Jewish people in Iran, tracing a legacy that began with Cyrus the Great liberating Jews from Babylonian captivity. While the Pahlavi Dynasty ushered in a "Golden Era" of prosperity and religious freedom, the 1979 Islamic Revolution radically shifted the landscape into one of hostility and strict religious law. Personal narratives and historical records highlight Iran’s role as a refuge for Jewish orphans during World War II, contrasted against the later execution of industrialist Habib Elghanian. Modern accounts describe the mass exodus of the community and the challenges of maintaining cultural identity through food and memory in the diaspora. Ultimately, the collection portrays a complex evolution from ancient Persian-Jewish harmony to a contemporary era of political tension and restrictive social change. | 17m 50s | ||||||
| 2/26/26 | 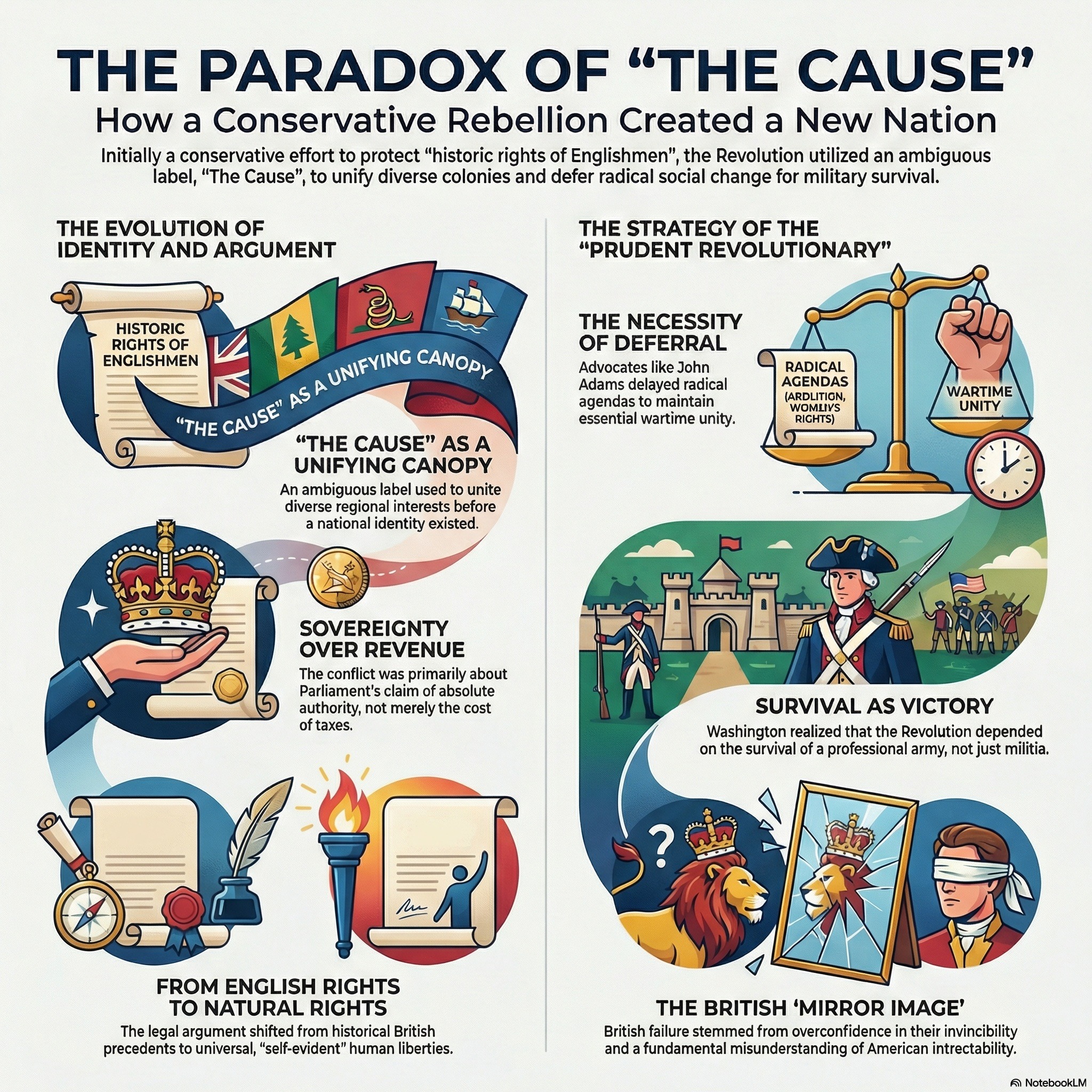 The American Revolution Was A Toxic Divorce The American Revolution Was A Toxic Divorce | This podcast examines the American Revolution by analyzing the divergent political perspectives of the British monarchy and the colonial rebels. While the National Archives provides the foundational text of the Declaration of Independence, other scholarly works explore the ideological origins of the conflict, focusing on the colonists' fear of parliamentary corruption and the Crown’s insistence on absolute sovereignty. Historical narratives highlight the leadership of George Washington and the strategic failures of King George III, whose inability to address grievances transformed a colonial dispute into a global war. The podcast also provides a window into the logistical hardships of the Continental Army and the complex internal debates regarding slavery and national unity. Ultimately, the collection portrays the revolution as a pivotal transformation that shifted the foundation of governance from monarchical authority to natural rights and popular consent. | 18m 00s | ||||||
| 2/25/26 | 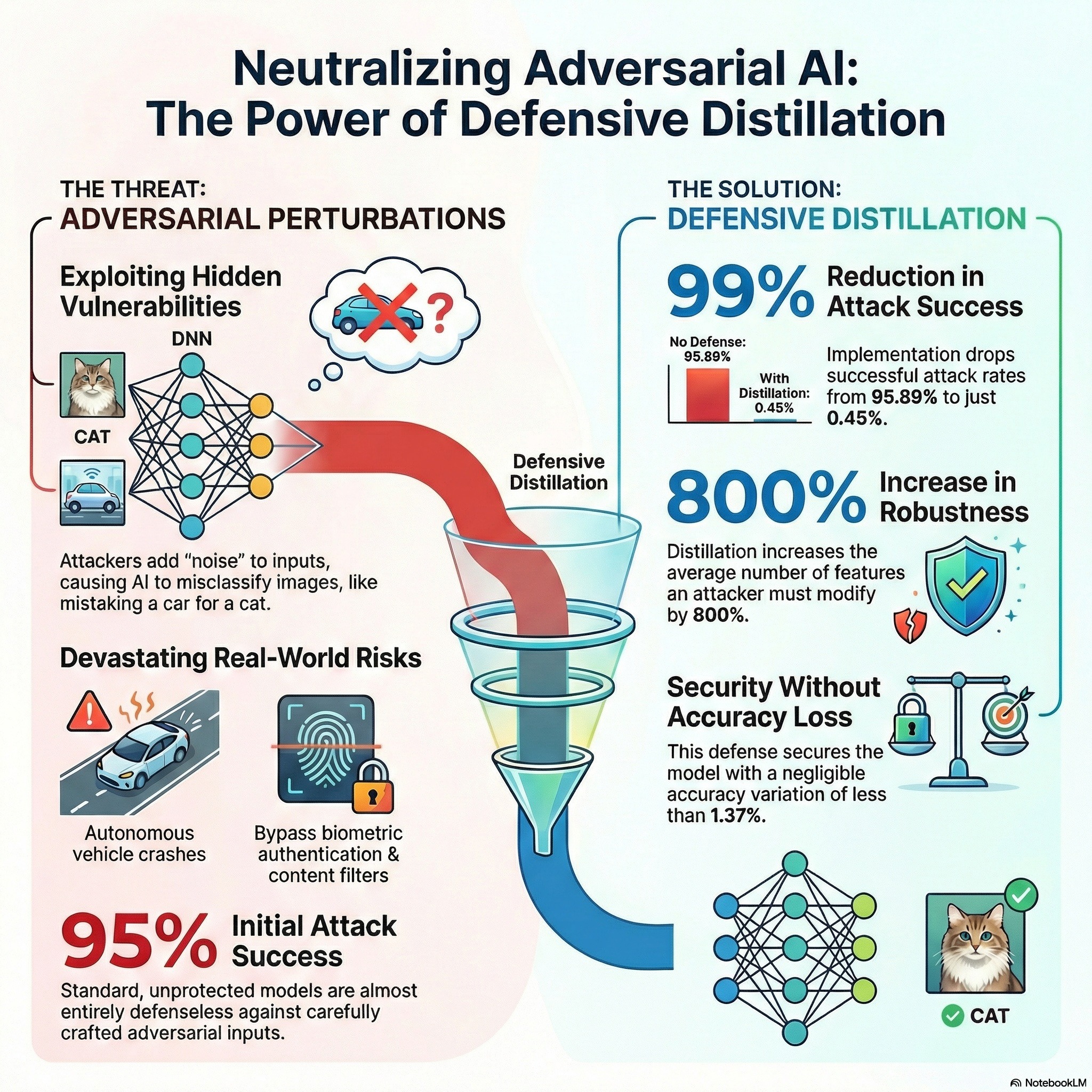 Security Analytics - Podcast 05 - Adversarial Machine Learning Security Analytics - Podcast 05 - Adversarial Machine Learning | These sources examine the security of deep neural networks by focusing on the identification and mitigation of adversarial attacks. Research highlights how evasion attacks exploit model vulnerabilities during deployment by using subtle, human-indistinguishable perturbations to cause misclassifications. To counter these threats, authors propose formal verification frameworks that utilize mathematical optimization and reachability analysis to prove model robustness. Additionally, defensive strategies like adversarial training and defensive distillation are shown to reduce a model's sensitivity to input variations. The literature emphasizes a critical trade-off between a system's computational scalability, its mathematical completeness, and its overall accuracy. Ultimately, these works categorize existing defense methodologies into a structured taxonomy to guide future developments in AI security. | 15m 50s | ||||||
| 2/24/26 | 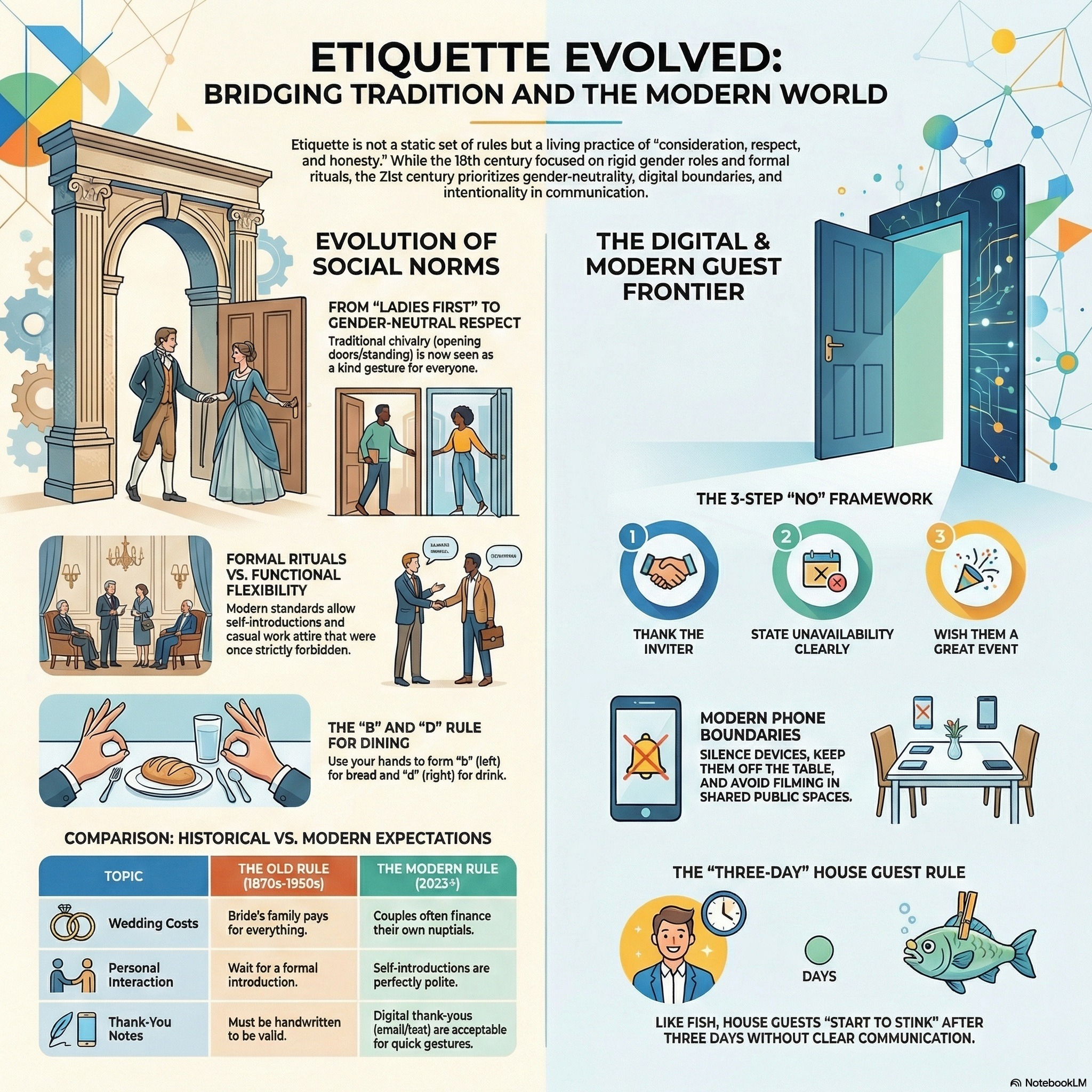 The Lost Art Of Traditional Western Etiquette The Lost Art Of Traditional Western Etiquette | This podcast explores the evolution and application of social etiquette, ranging from historical Edwardian customs to modern digital manners. They provide practical guidance on interpersonal behavior, such as chivalrous dating acts, proper introductions based on seniority, and effective ways to politely decline invitations. A significant focus is placed on modern technology, offering specific rules for cell phone usage and navigating the complexities of American tipping culture. Additionally, the texts address lifestyle standards including professional dress codes, houseguest responsibilities, and the importance of maintaining kindness and composure in daily interactions. Overall, the collection serves as a comprehensive manual for navigating social, professional, and domestic life with grace and respect. | 37m 01s | ||||||
| 2/24/26 | 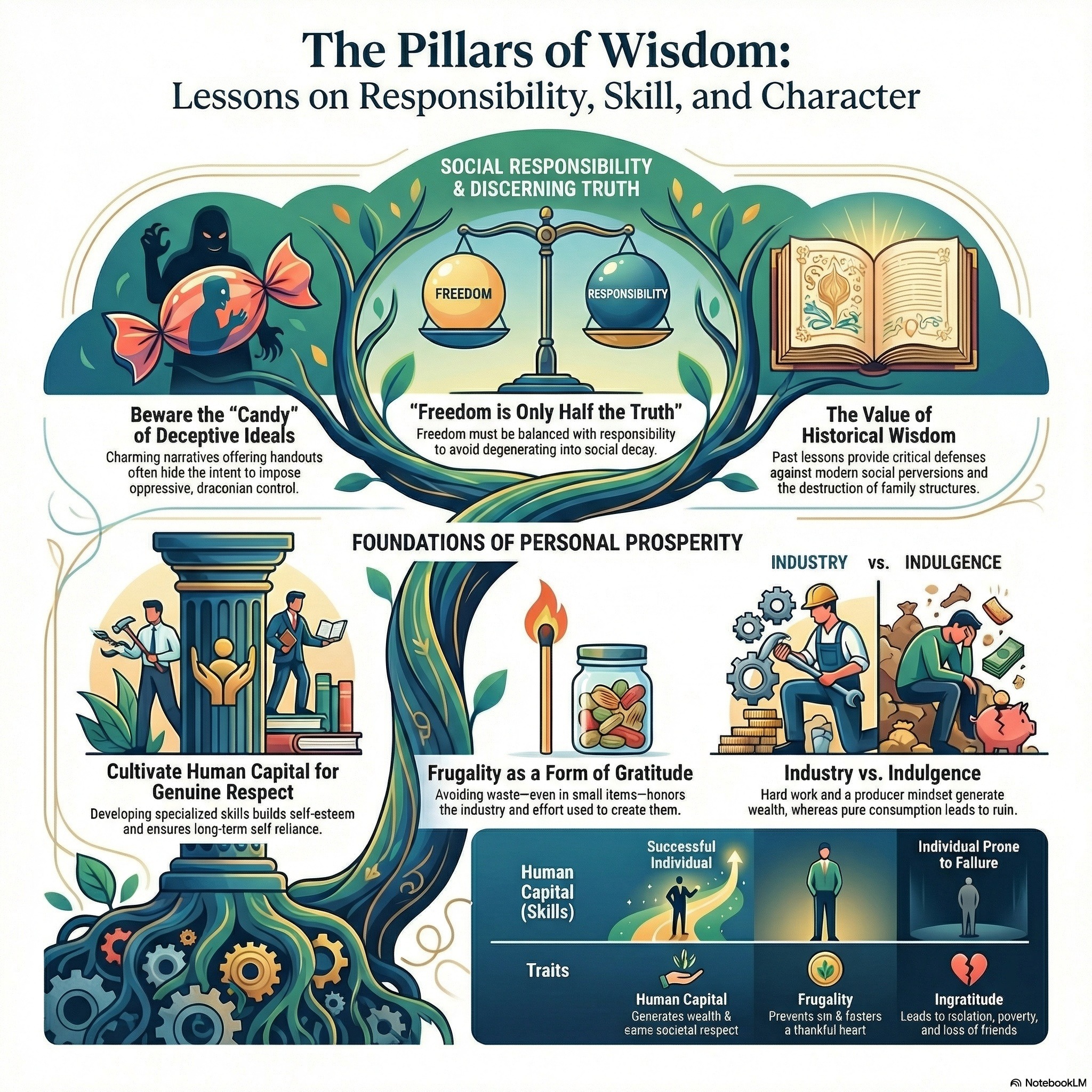 The Matchstick, The Hook, & The Snakes The Matchstick, The Hook, & The Snakes | These moral fables emphasize the vital connection between personal responsibility, gratitude, and discerning wisdom. The first story illustrates how human capital and frugality are more valuable than inherited wealth, as a spoiled son only finds true purpose after losing everything and recognizing his father's foresight. In the second narrative, the consequences of gossip and the danger of freedom without accountability are explored through the manipulation of two oak trees by malicious crows. The third account warns against deceptive ideologies and the loss of liberty, using charming snakes to symbolize how societies can be hypnotized into surrendering their values. Finally, the account of the merchant and the matchstick reinforces that attentiveness to small details and the rejection of wastefulness form the foundation of great generosity. Together, these texts argue that a functional society relies on individuals who value past wisdom, practice self-discipline, and resist the influence of predatory social forces. | 26m 39s | ||||||
| 2/20/26 | 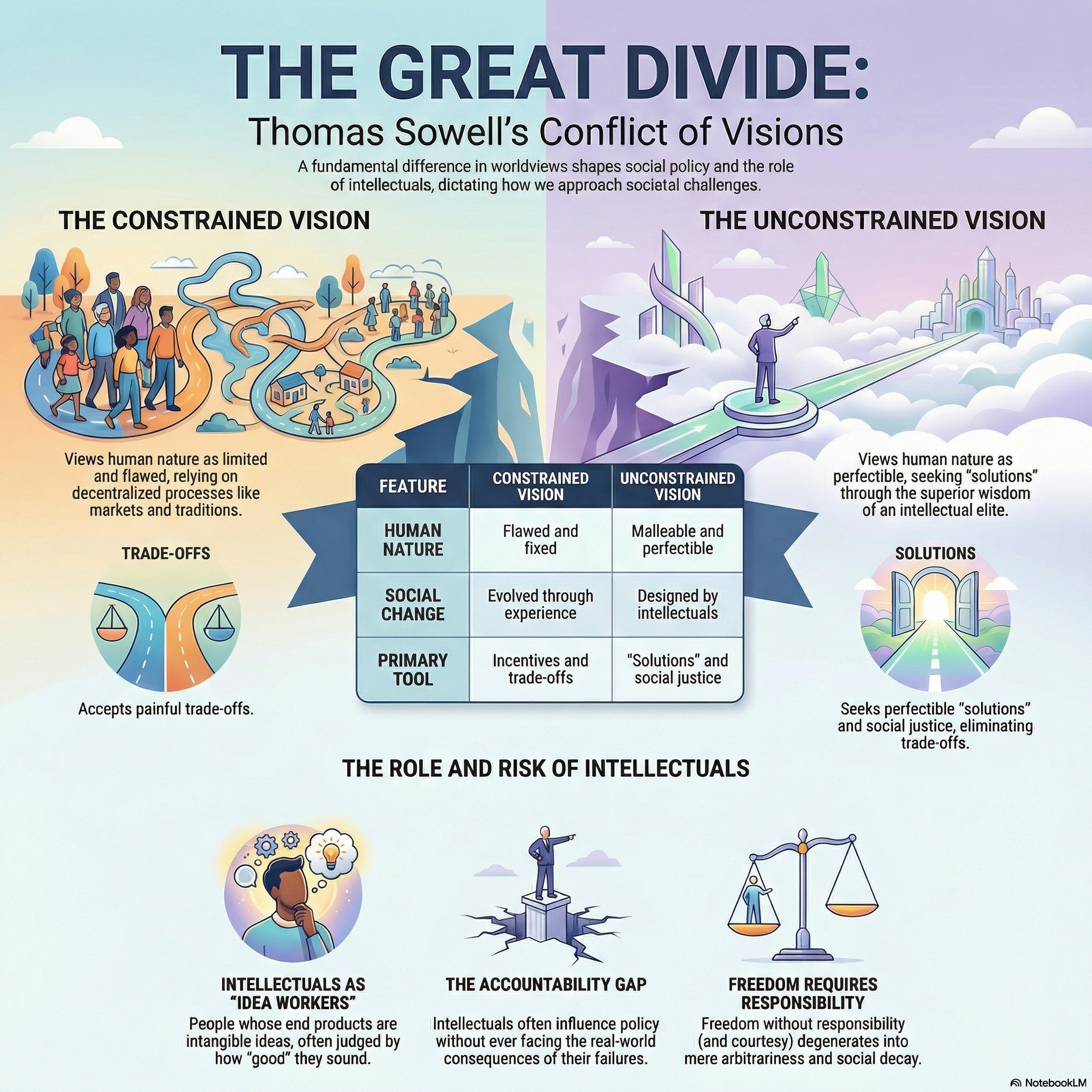 How Intellectuals Dismantle Society From Within How Intellectuals Dismantle Society From Within | This podcast profiles the life and philosophy of Thomas Sowell, a prominent economist who critiques the "anointed" class of intellectuals for prioritizing abstract theories over empirical reality. The texts argue that modern intellectuals often champion a vision of "liberation" from traditional social restraints, which Sowell contends has historically led to disastrous outcomes like family disintegration and increased crime. Through books like Intellectuals and Society, he highlights a dangerous lack of accountability among idea workers who influence public policy without facing the consequences of their failed prescriptions. Parables within the collection further illustrate the risks of abandoning ancestral wisdom and the necessity of pairing personal freedom with individual responsibility. Ultimately, the sources celebrate Sowell’s commitment to hard data and his belief that the prosperity of ordinary people depends on a refuge from the presumptuous social engineering of elites. | 37m 51s | ||||||
| 2/20/26 | 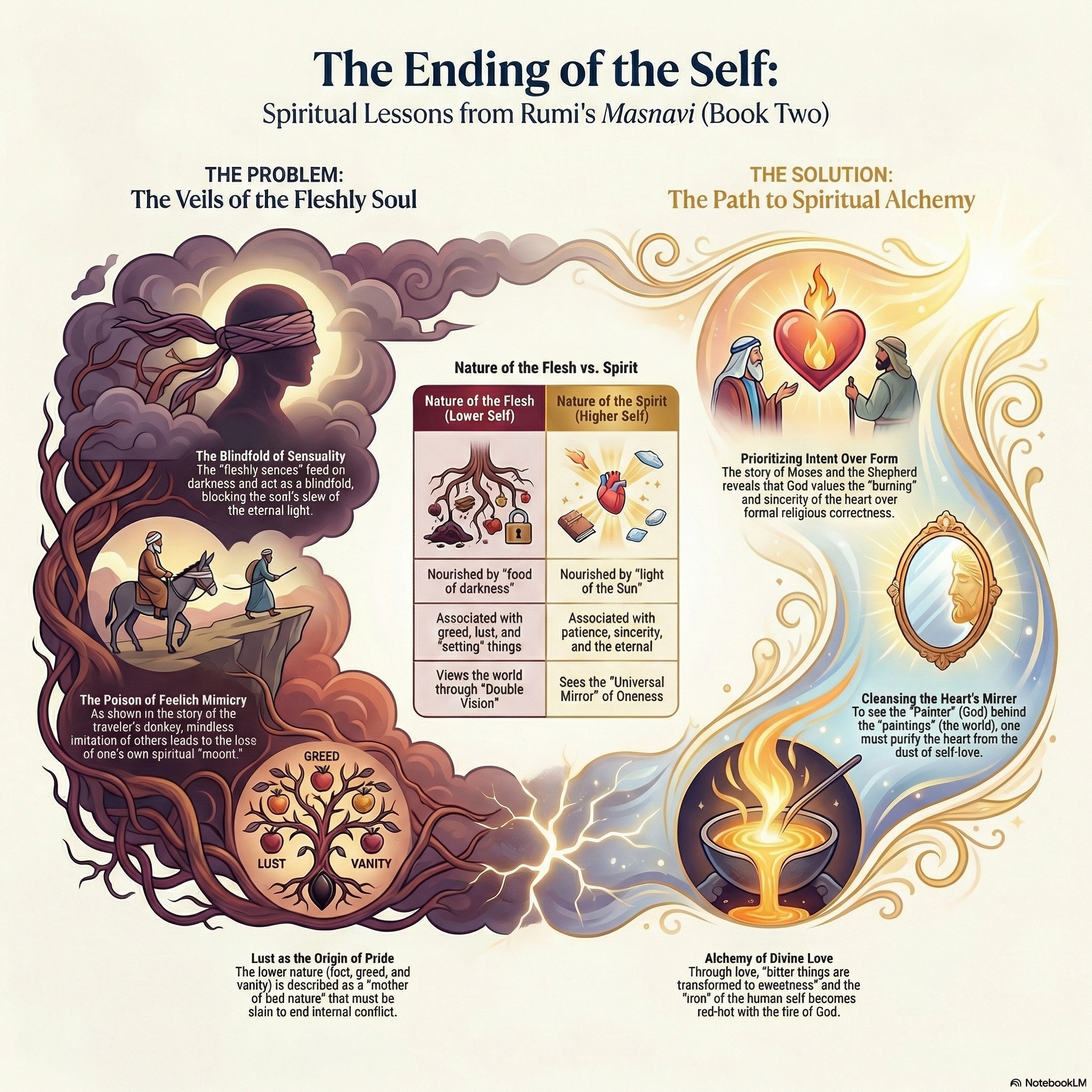 Rumi’s Animals Roast Your Ego Rumi’s Animals Roast Your Ego | This podcast examines the mystical and pedagogical dimensions of Sufism, primarily through the symbolic Quranic narrative of Moses and the spiritual guide Khidr. Scholars and poets like Rumi use this story to illustrate the master-disciple relationship, emphasizing that true wisdom often transcends external law and human logic. The podcast explores how mystical "unveiling" allows practitioners to move beyond physical senses to perceive divine realities and achieve spiritual purity. Further commentary connects these Islamic traditions to broader philosophical frameworks, including Neoplatonism and historical hagiographies of various saints. Ultimately, the collection highlights the transformation of the soul from worldly attachment to a state of divine union and contentment. | 17m 17s | ||||||
| 2/16/26 | 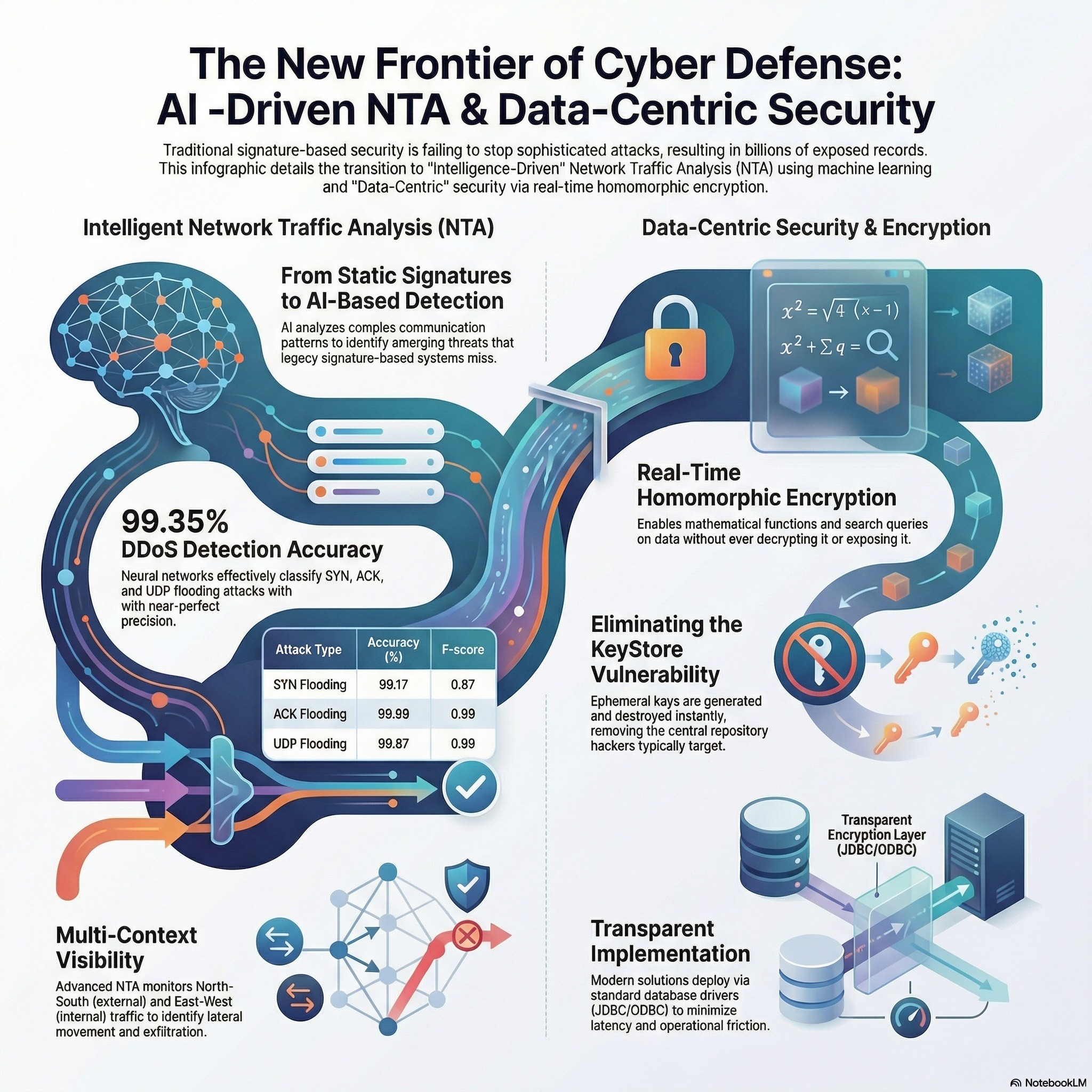 Security Analytics - Podcast 04 - Machine Learning Security Applications For Business Security Analytics - Podcast 04 - Machine Learning Security Applications For Business | This podcast investigates advanced methods for enhancing cybersecurity through the application of machine learning. The primary study details the creation of a neural network specifically designed to identify and categorize DDoS flooding attacks, such as SYN and UDP flooding, with high precision. By utilizing a 24-106-5 architecture, the researchers achieved an accuracy rate of over 95% in both simulated and laboratory environments. A second source complements this by exploring the detection of pivoting activity, using statistical correlation and Principal Component Analysis to identify malicious movements within a network. Together, these sources demonstrate how automated data analysis can distinguish between legitimate traffic and sophisticated threats. Consequently, the findings suggest that neural networks and algorithmic feature extraction are essential for maintaining robust, modern information security systems. | 14m 35s | ||||||
| 2/8/26 | 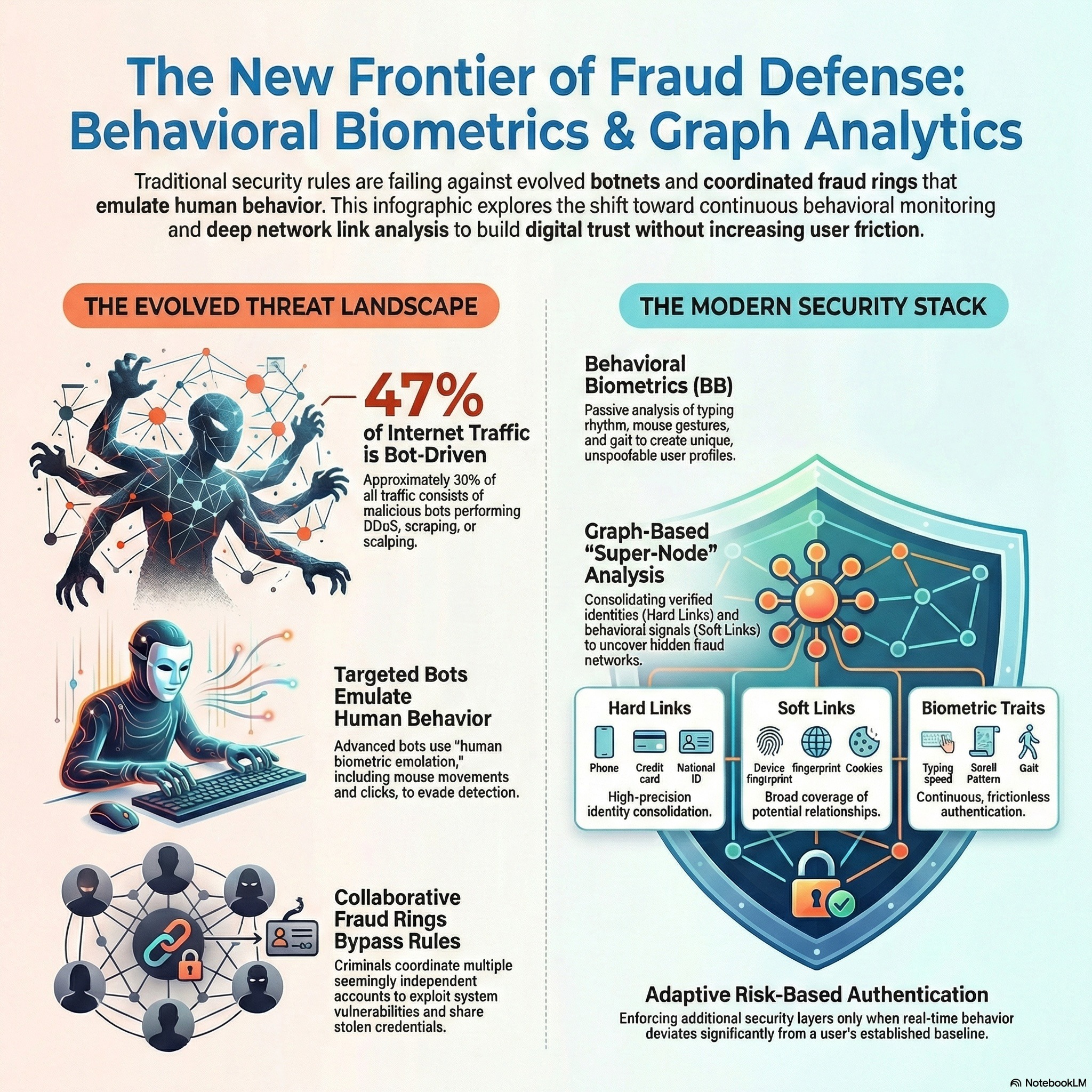 Security Analytics - Podcast 03 - Fraud, Biometrics, & Bots Security Analytics - Podcast 03 - Fraud, Biometrics, & Bots | Modern cybersecurity faces sophisticated threats like botnets, insider attacks, and fraud. Organizations utilize Behavioral Biometrics and UEBA to establish baseline user profiles. By analyzing unique patterns like keystroke dynamics, these systems enable real-time defense. | 18m 59s | ||||||
| 2/4/26 | 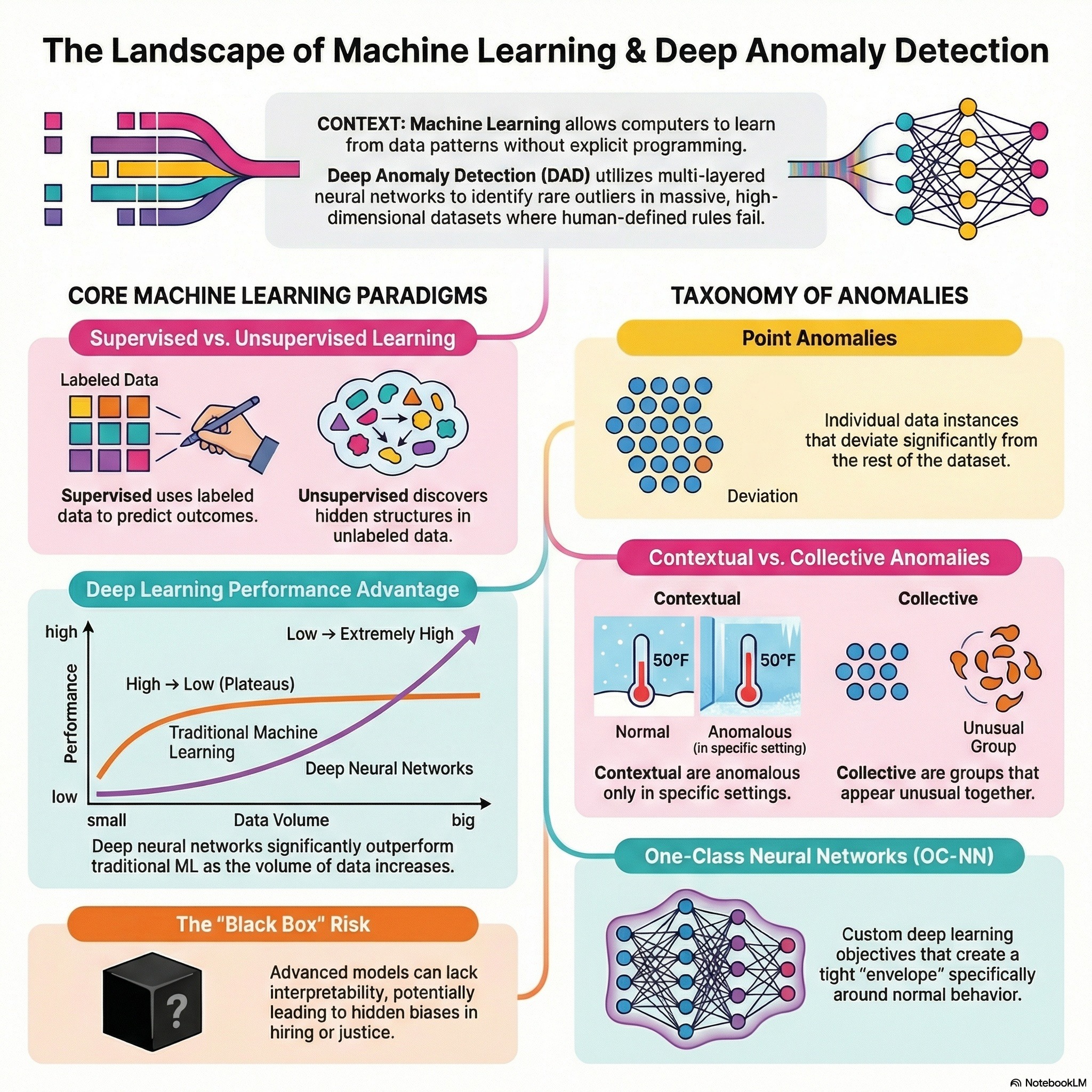 Security Analytics - Podcast 02 - Machine Learning Security Analytics - Podcast 02 - Machine Learning | This module explores data mining, visualization, and machine learning concepts for security analytics. It details anomaly detection using network traffic. It clarifies machine learning techniques such as Regressions, Näive Bayes, Decision Trees, Random Forests, and KNN. It goes over supervised and unsupervised machine learning approaches. | 17m 27s | ||||||
Showing 25 of 70
Sponsor Intelligence
Sign in to see which brands sponsor this podcast, their ad offers, and promo codes.
Chart Positions
1 placement across 1 market.
Chart Positions
1 placement across 1 market.