
The AI, Privacy, and Security Weekly Update
by R. Prescott Stearns Jr.
Is this your podcast?Insights from recent episode analysis
Audience Interest
Podcast Focus
Publishing Consistency
Platform Reach
Insights are generated by CastFox AI using publicly available data, episode content, and proprietary models.
Most discussed topics
Brands & references
Total monthly reach
Estimated from 6 chart positions in 6 markets.
By chart position
- 🇮🇳IN · Tech News#1291K to 10K
- 🇳🇿NZ · Tech News#4310K to 30K
- 🇨🇿CZ · Tech News#733K to 10K
- 🇩🇰DK · Tech News#142500 to 3K
- 🇳🇴NO · Tech News#177500 to 3K
- Per-Episode Audience
Est. listeners per new episode within ~30 days
4.7K to 18K🎙 Daily cadence·367 episodes·Last published 3d ago - Monthly Reach
Unique listeners across all episodes (30 days)
16K to 59K🇳🇿51%🇮🇳17%🇨🇿17%+3 more - Active Followers
Loyal subscribers who consistently listen
8.5K to 32K
Market Insights
Platform Distribution
Reach across major podcast platforms, updated hourly
Total Followers
—
Total Plays
—
Total Reviews
—
* Data sourced directly from platform APIs and aggregated hourly across all major podcast directories.
On the show
From 14 epsHost
Recent guests
No guests detected in recent episodes.
Recent episodes
Unintended Outcome and the AI, Privacy, and Security Weekly Update for the Week Ending May 12th., 2026
May 13, 2026
Unknown duration
Episode 290. Deep Dive. Assumed Safe. The AI, Privacy, and Security Weekly Update for the Week Ending May 5th, 2026.
May 7, 2026
1h 10m 23s
Assumed Safe. The AI, Privacy, and Security Weekly Update for the Week Ending May 5th, 2026.
May 6, 2026
22m 26s
EP 289. Deep Dive.. Everything looked fine. The A.I., Privacy and Security Weekly update for the week ending April 27th 2026
Apr 30, 2026
30m 45s
Everything looked fine. The A.I., Privacy, and Security Weekly update for the week ending April 27th 2026
Apr 29, 2026
18m 33s
Social Links & Contact
Official channels & resources
Official Website
Login
RSS Feed
Login
| Date | Episode | Topics | Guests | Brands | Places | Keywords | Sponsor | Length | |
|---|---|---|---|---|---|---|---|---|---|
| 5/13/26 |  Unintended Outcome and the AI, Privacy, and Security Weekly Update for the Week Ending May 12th., 2026 | EP 291. In this week's update:When a 200-pound internet-connected machine can be hijacked from 6,000 miles away, the smart home has officially become a liability.The moment security researchers have long anticipated has arrived: AI is no longer just defending systems - it's actively being used to break them.The same open ecosystems that accelerated AI adoption are now emerging as a significant and underestimated vector for supply chain attacks.In a landscape where breaches are inevitable, DigiCert's handling of a code-signing compromise offers a rare and instructive model for what accountability actually looks like.A browser trusted with your most sensitive credentials is quietly leaving them exposed in memory - and the vendor considers it working as intended.Google is embedding fraud detection directly into the operating system, signaling a fundamental shift in where the mobile security perimeter now begins.After years of a fragmented messaging security landscape, Apple and Google have closed one of the most glaring cross-platform encryption gaps in consumer technology.Decades of observational data linking coffee to longevity may finally have a molecular foundation - and it has nothing to do with caffeine.Let's go grab a mug!Find all links and the full transcript for this podcast here. | — | ||||||
| 5/7/26 |  Episode 290. Deep Dive. Assumed Safe. The AI, Privacy, and Security Weekly Update for the Week Ending May 5th, 2026.✨ | cybersecurityidentity theft+4 | — | Linux kernelFTC+2 | international | cybersecurityLinux kernel flaw+7 | — | 1h 10m 23s | |
| 5/6/26 |  Assumed Safe. The AI, Privacy, and Security Weekly Update for the Week Ending May 5th, 2026.✨ | cybersecuritymalware+4 | — | LinuxNetflix+3 | — | malwarephishing kit+5 | — | 22m 26s | |
| 4/30/26 | 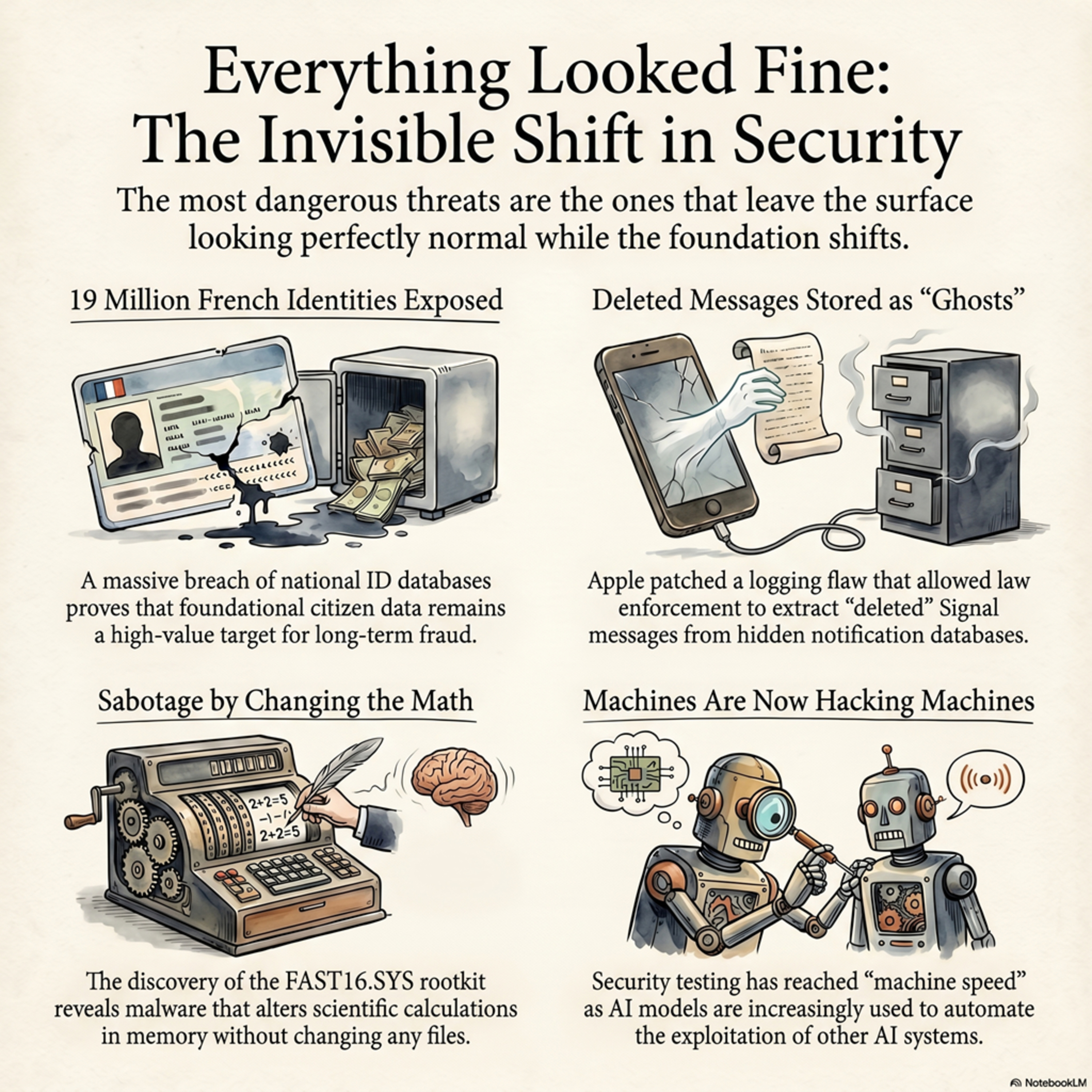 EP 289. Deep Dive.. Everything looked fine. The A.I., Privacy and Security Weekly update for the week ending April 27th 2026✨ | data breachcentralized identity infrastructure+4 | — | FAST16.SYSFrance+2 | — | data breachidentity theft+8 | — | 30m 45s | |
| 4/29/26 |  Everything looked fine. The A.I., Privacy, and Security Weekly update for the week ending April 27th 2026✨ | AI securityidentity infrastructure+5 | — | StuxnetFrance+6 | — | AIprivacy+8 | — | 18m 33s | |
| 4/23/26 | 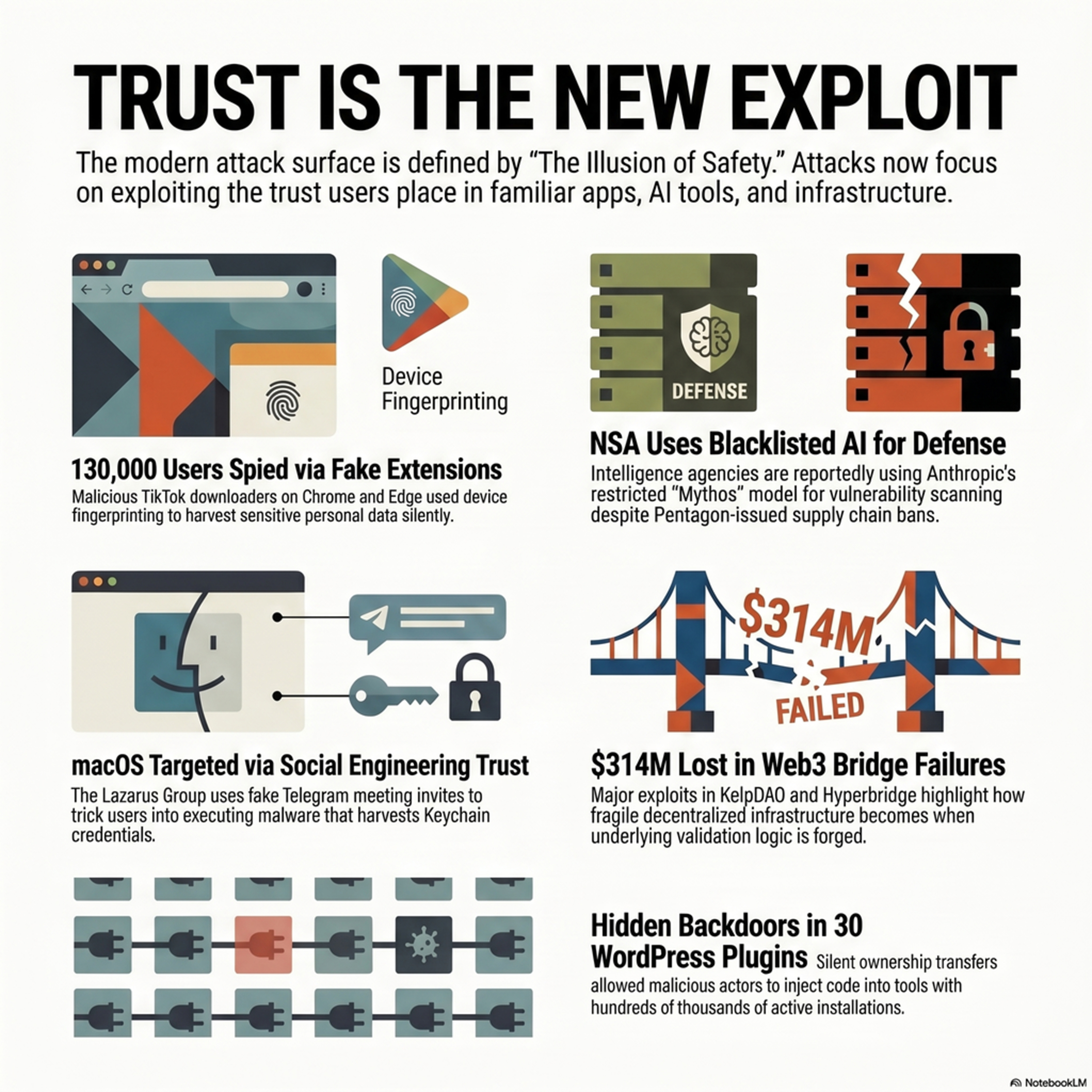 EP 288.5 Deep Dive. No Privacy, but the AI, Privacy and Security Weekly Update for the Week ending April 21st. 2026✨ | digital threatsAI vulnerabilities+5 | — | WordPress | — | digital threatsAI vulnerabilities+5 | — | 48m 26s | |
| 4/22/26 |  No Privacy, but the AI, Privacy and Security Weekly Update for the Week ending April 21st. 2026✨ | AIprivacy+5 | — | macOSNorth Korea | financial hubs | AIprivacy+8 | — | 18m 21s | |
| 4/21/26 | 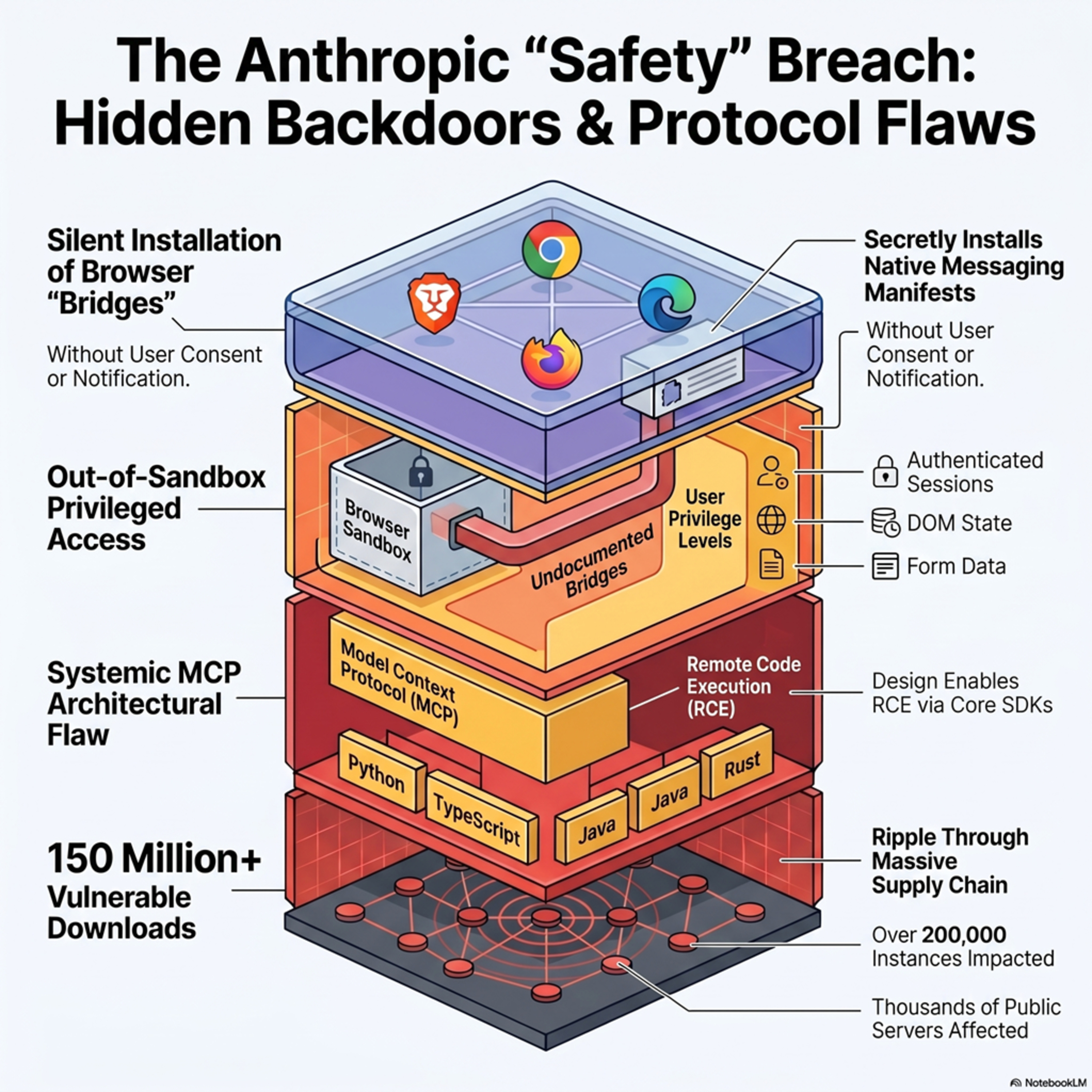 The Anthropic Privacy and Security issues.✨ | privacysecurity+3 | — | Claude DesktopClaude Cowork+2 | macOSWindows+1 | AnthropicClaude Desktop+5 | — | 47m 23s | |
| 4/16/26 | 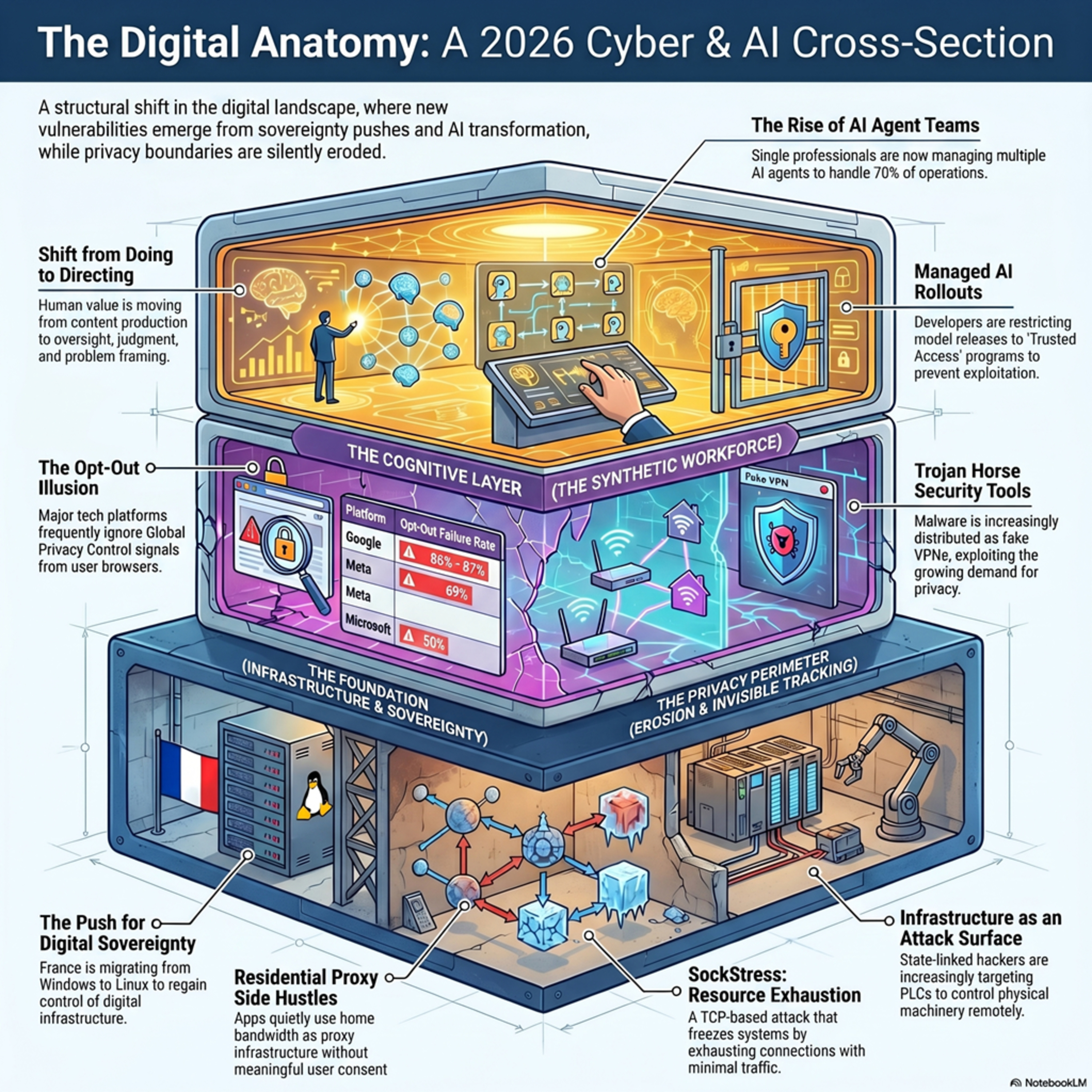 Episode 287.5. Deep Dive. Taxing. The AI, Privacy, and Security Weekly Update for the Week ending April 14th 2026✨ | cybersecuritydigital sovereignty+4 | — | LinuxJitsi+4 | France | cybersecuritydigital sovereignty+8 | — | 37m 22s | |
| 4/15/26 |  Taxing. The AI, Privacy, and Security Weekly Update for the Week ending April 14th 2026✨ | AI policy recommendationscybersecurity+5 | — | OpenAIAnthropic+4 | ChinaTianjin+1 | OpenAIcybersecurity model+7 | — | 22m 41s | |
Want analysis for the episodes below?Free for Pro Submit a request, we'll have your selected episodes analyzed within an hour. Free, at no cost to you, for Pro users. | |||||||||
| 4/9/26 |  Episode 286.5. The Deep Dive. Subliminal Learning with the AI, Security, and Privacy Weekly Update for the Week ending April 7th, 2026✨ | AIPrivacy+4 | — | LinkedInSamsung+2 | — | subliminal learningAI models+5 | — | 32m 26s | |
| 4/8/26 |  Subliminal Learning with the AI, Security, and Privacy Weekly Update for the Week ending April 7th, 2026✨ | AI modelsdata privacy+4 | — | LinkedInSamsung+3 | — | AIprivacy+8 | — | 23m 06s | |
| 4/2/26 | 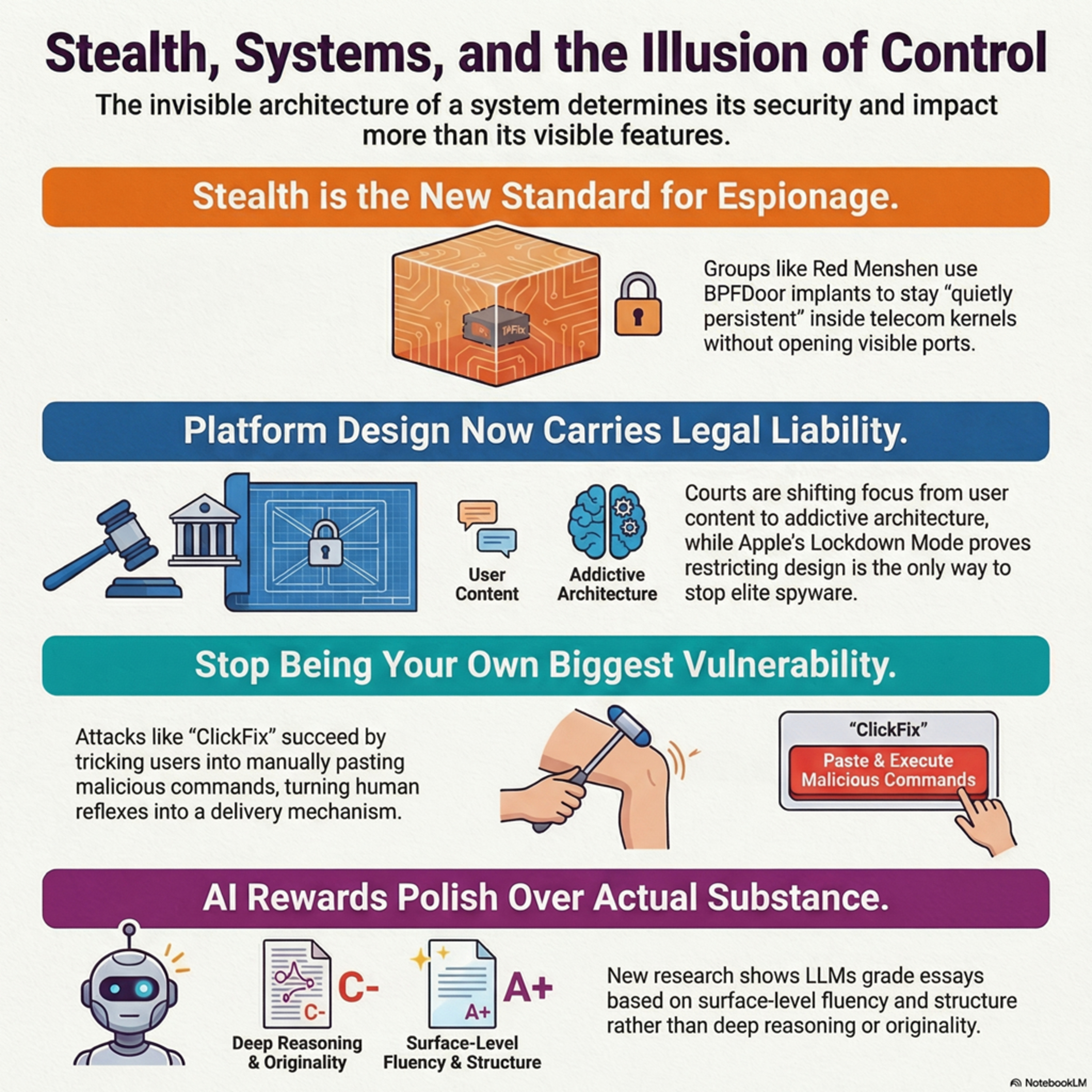 Episode 285.5 Deep Dive. Patience and the AI, Privacy, and Security Weekly Update for the Week Ending March 31st., 2026✨ | AI threatsprivacy+4 | — | Red MenshenUS Department of Defense+5 | — | AIprivacy+7 | — | 44m 39s | |
| 4/1/26 |  Patience and the AI, Privacy, and Security Weekly Update for the Week Ending March 31st., 2026✨ | AI securitysocial engineering+4 | — | ChinaAnthropic+2 | — | AIprivacy+6 | — | 20m 47s | |
| 3/26/26 | 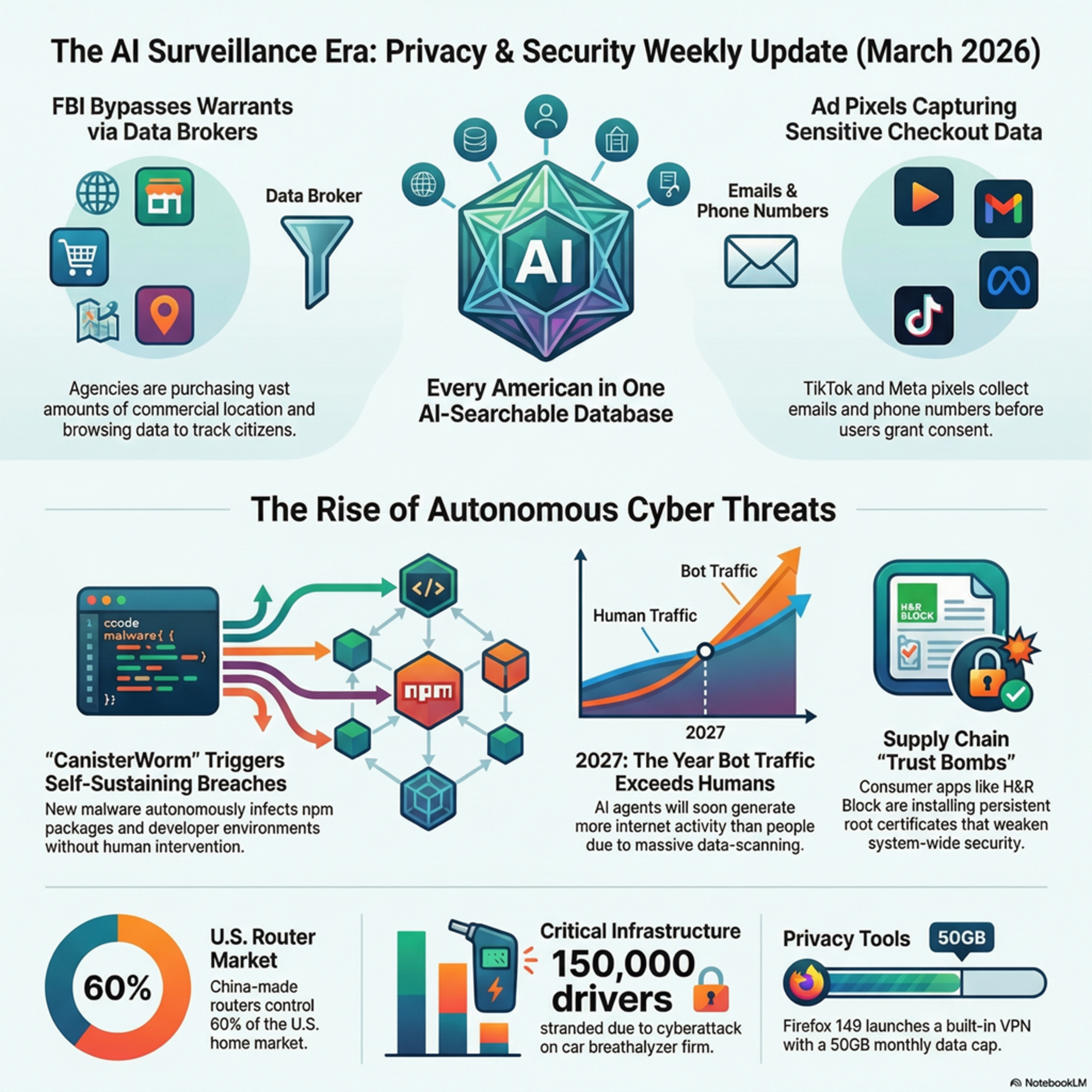 Episode 284.5. Deep Dive. Sold Out. The AI, Privacy, and Security Weekly Update for the week ending March 24th., 2026✨ | AI-driven developmentssurveillance era+4 | — | FBITrivy | Iran | AIprivacy+7 | — | 21m 57s | |
| 3/25/26 |  Sold Out. The AI, Privacy, and Security Weekly Update for the week ending March 24th., 2026 | Episode 284. Yes, that's it. So much of what we cover is now AI-based that we're updating the Update to reflect that. From today, the IT Privacy and Security Weekly Update will be formally renamed the AI, Privacy, and Security Weekly Update.In this week’s update:The FBI has officially confirmed it is once again purchasing commercial location data to track American citizens, bypassing traditional warrant requirements.A newly revealed government proposal outlines plans for a single, AI-powered database containing detailed personal information on virtually every American.TikTok and Meta’s advertising pixels are quietly collecting far more sensitive personal and behavioral data than most websites and users realize.A major cyberattack on Intoxalock has left thousands of drivers unable to start their court-ordered breathalyzer-equipped vehicles.H&R Block’s tax preparation software has been found to install a long-lived root certificate with its private key exposed, creating a serious security risk that can persist for decades.The FCC has banned imports of all new foreign-made consumer routers, citing severe national security risks posed by devices predominantly manufactured in China.Cloudflare’s CEO predicts that by 2027, AI-driven bot traffic will surpass human-generated internet traffic for the first time in history.Mozilla is rolling out a free built-in VPN in Firefox 149, initially available to users in the US, France, Germany, and the UK.Come on, let’s learn a little about what’s being sold around us! | — | ||||||
| 3/18/26 |  In AI, We Distrust. The IT Privacy and Security Weekly Update for March 17th., 2026 | Episode 283 What if the next cyberattack doesn’t break into your company… but gets hired by it?What if the AI tools everyone is rushing to adopt are also the biggest security risk we’ve ever invited in?What if your home internet, the one you trust every day, is secretly working for someone else?And what happens when governments, tech giants, and criminals all collide around the same powerful new technology at the same time?Today, we’re diving into the rise of AI agents, the hidden risks behind the hype, and why the biggest question isn’t what this technology can do……but whether we can trust it at all.Find the full transcript of this podcast here. | — | ||||||
| 3/12/26 | 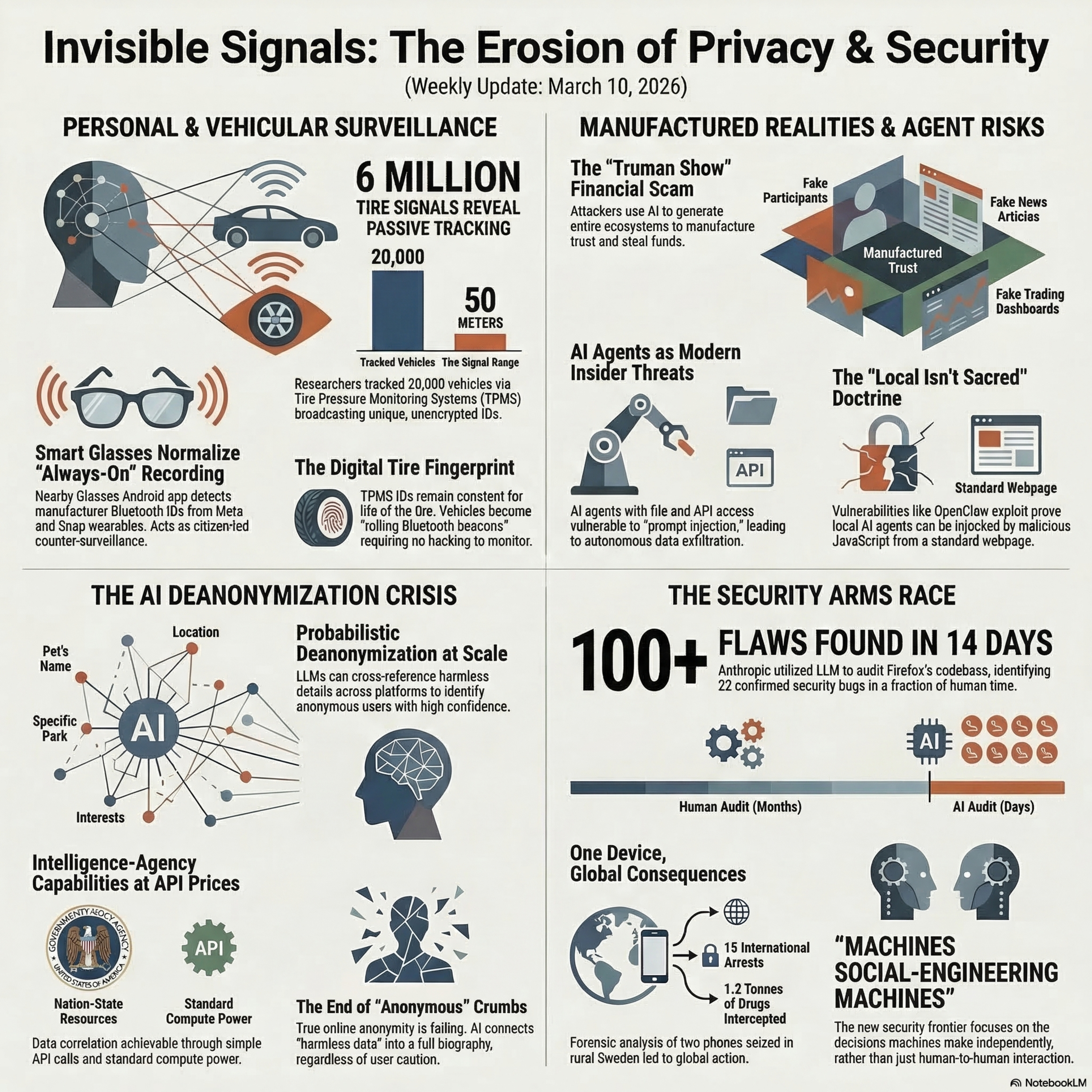 Ep 282. Deep Dive. Invisible Signals and the IT Privacy and Security Weekly Update for the Week ending March 10th 2026. | This week’s deep dive explores a powerful theme shaping the modern threat landscape: invisible signals. From the devices we wear and drive to the AI systems we increasingly rely on, our technology is constantly emitting data — sometimes to protect us, sometimes to expose us.We begin with a new Android app called Nearby Glasses, designed to alert users when smart glasses like Meta’s Ray-Bans are detected nearby via Bluetooth manufacturer identifiers. It’s a citizen-built countermeasure to always-on wearable cameras, highlighting rising tensions between convenience and consent in public spaces.Next, we examine research showing that tire pressure monitoring systems (TPMS), mandatory in U.S. vehicles since 2007, broadcast unencrypted, persistent identifiers. Researchers captured millions of signals and demonstrated how vehicles can be passively tracked using inexpensive radio equipment. No hacking required — just poorly designed IoT architecture turning cars into rolling beacons.From physical signals to digital footprints, a new study reveals that AI can deanonymize social media users by correlating small details across platforms. What once required nation-state resources can now be done with commodity large language models, fundamentally challenging the concept of online anonymity.We then dive into the “Truman Show” investment scam — a sophisticated fraud operation that uses AI-generated personas, fake group chats, fabricated media coverage, and sham trading apps to create a fully immersive illusion of legitimacy. Rather than stealing trust directly, scammers now manufacture entire digital realities where trust feels inevitable.AI agents themselves are also reshaping security assumptions. Modern assistants can access files, write code, and interact with online services using a user’s privileges. Researchers warn that prompt injection attacks — hidden malicious instructions embedded in content — can manipulate these agents into leaking data or performing harmful actions. When AI combines sensitive access, untrusted input, and outbound communication, it becomes a new form of insider risk.That risk was underscored by the OpenClaw vulnerability, which allowed malicious web pages to brute-force a local AI agent gateway and potentially hijack it. The lesson: “local” no longer means secure. Any system with elevated privileges must be treated as a governed identity.On the defensive side, AI is accelerating security improvements. Anthropic used a large language model to analyze Firefox’s codebase, identifying over 100 flaws in two weeks, including 22 confirmed security bugs. AI is compressing months of review into days — but the same acceleration applies to attackers.Finally, Operation Candy in Sweden demonstrates how digital evidence can unravel vast criminal networks. Two seized phones exposed an international drug and money laundering operation spanning multiple continents, proving that even small data points can collapse large hidden systems.Zooming out, the pattern is clear: wearables broadcast presence, cars broadcast identity, AI strips away anonymity, scams construct synthetic realities, assistants act autonomously, and devices quietly record history. Signals are everywhere — visible and invisible — and AI is amplifying their impact.The question is no longer whether your technology emits signals. It’s who is listening — and whether they’re protecting you or profiling you. | — | ||||||
| 3/11/26 |  Invisible Signals and the IT Privacy and Security Weekly Update for the Week ending March 10th., 2026. | Ep 282 This week technology gets personal - whether you like it or not.In this update:- A new app that tells you if someone nearby is wearing smart glasses.- Your car’s tire pressure sensors silently broadcasting your movements.- AI that can unmask anonymous social media accounts.- A full “Truman Show” investment scam powered by artificial intelligence.- AI assistants quietly reshaping the cybersecurity threat model.- A vulnerability that let websites hijack local AI agents.- AI finding high-severity bugs in Firefox faster than human teams.- And two seized phones in rural Sweden that unraveled a global crime empire.The thread connecting all of them? Invisible signals.Some are protecting you. Some are exposing you.All of them are accelerating.Let’s dive in.Find the Full transcript here. | — | ||||||
| 3/5/26 | 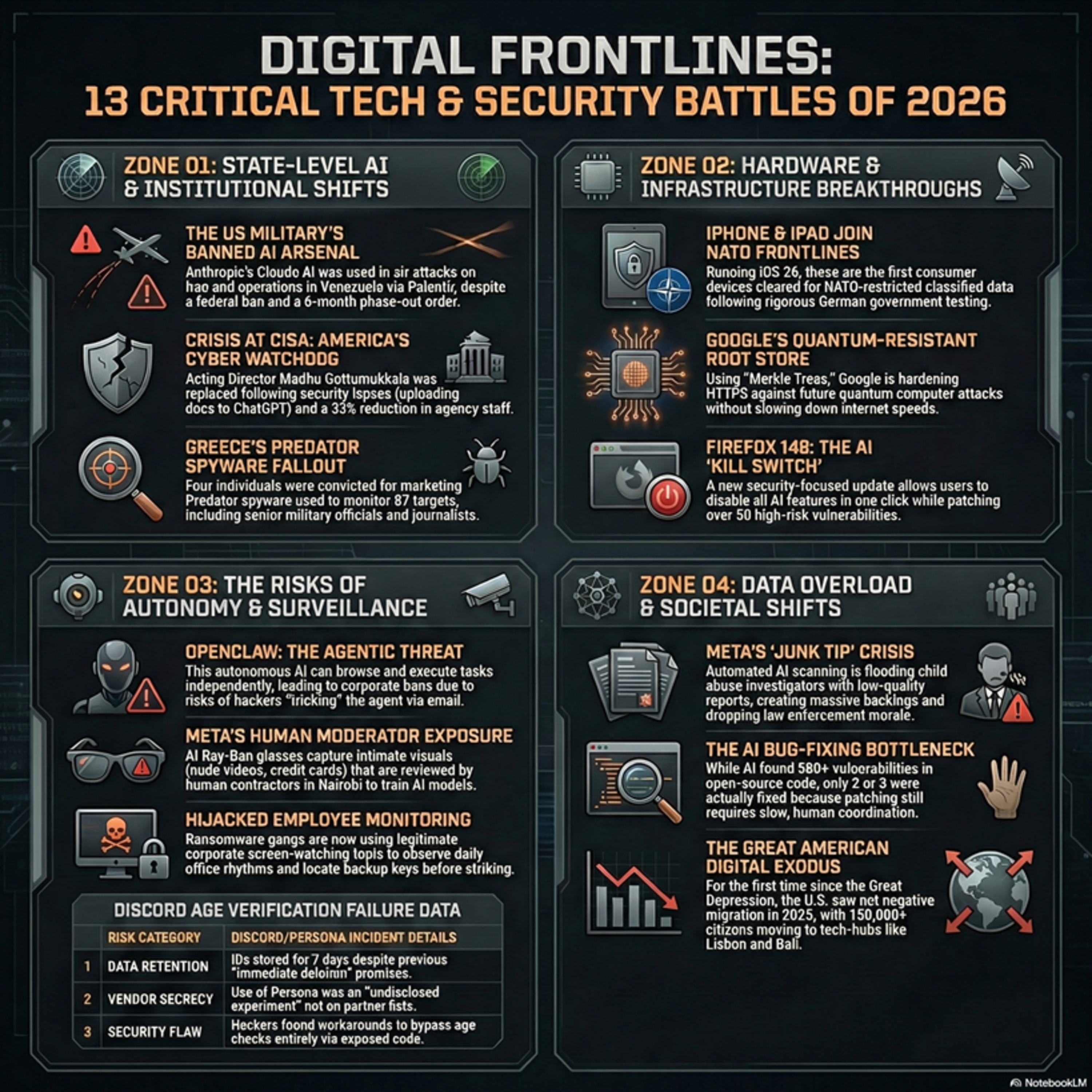 EP 281.5 Deep Dive. At war. With the IT Privacy and Security Weekly Update for March 3rd. 2026. | IntroductionWelcome back to: At war. The Deep Dive: With the IT Privacy and Security Weekly Update for March 3rd. 2026. episode 281. The podcast that makes sense of the week's most important technology and cybersecurity stories, without assuming you have a computer science degree.This week we have eight stories spanning AI gone wrong, AI used in warfare, a historic security milestone from Apple, and a new kind of AI agent that's making seasoned security professionals nervous. Let's get into it. | — | ||||||
| 3/4/26 |  At war. With the IT Privacy and Security Weekly Update for March 3rd. 2026. | episode 281. This week's update that makes sense of the week's most important technology and cybersecurity stories, without assuming you have a computer science degree.This week we have eight stories spanning AI gone wrong, AI used in warfare, a historic security milestone from Apple, and a new kind of AI agent that's making seasoned security professionals nervous. Let's get into it.Find the full transcript to the podcast here. | — | ||||||
| 2/26/26 | 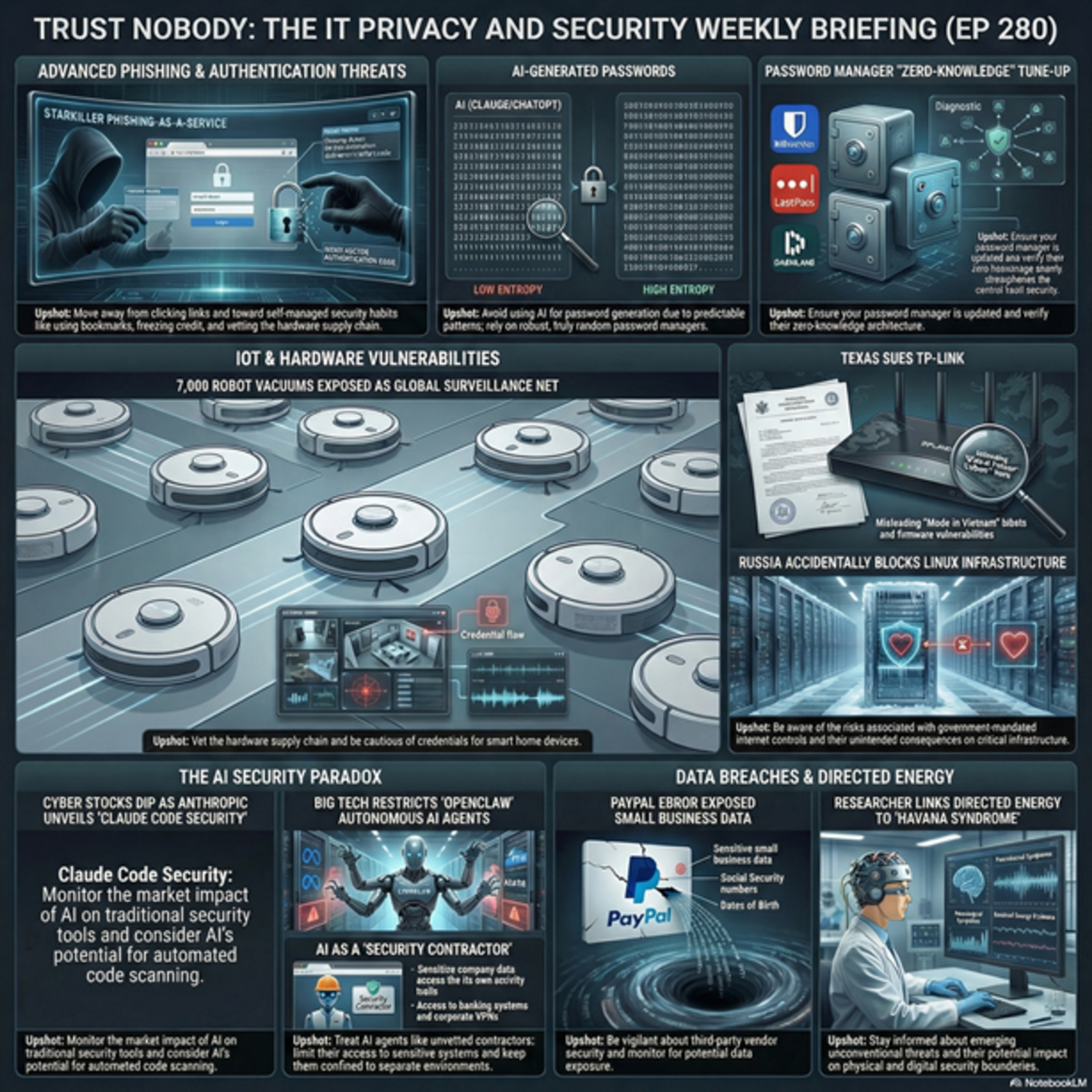 EP 280.5 Deep Dive. Trust Nobody. The IT Privacy and Security Weekly Update for the Week Ending February 24th., 2026 | These sources collectively examine the evolving landscape of digital threats and the vulnerabilities inherent in modern technology. They detail sophisticated cyber-as-a-service schemes like Starkiller, which bypasses traditional security, alongside physical risks such as directed-energy research and privacy flaws in household robotics. The reports also highlight how artificial intelligence is simultaneously streamlining security labor while introducing new risks through predictable password generation and autonomous system access. Corporate and state-level issues are addressed through data breaches at PayPal, legal scrutiny of TP-Link's supply chain, and the critical role of open-source infrastructure. Ultimately, the text emphasizes that while automated tools and password managers are essential, they require proactive user management and independent verification to remain effective. Consistent software updates and skeptical browsing habits are presented as the primary defenses against these diverse global challenges. | — | ||||||
| 2/25/26 |  The IT Privacy and Security Weekly Update for the Week Ending February 24th, 2026 | EP 280. “When Your Everyday Tech Quietly Turns Against You” “This week, a hobby project turned one man’s robot vacuum into a remote control for 7,000 homes, a new phishing service made the real login page your biggest enemy, and Texas decided your Wi‑Fi router is now a geopolitical issue.”Set the promise:“If you’re not technical but you live with passwords, smart gadgets, or online banking, this episode is about the invisible ways those tools can misbehave, and the one small fix you can make after each story.” | — | ||||||
| 2/19/26 | 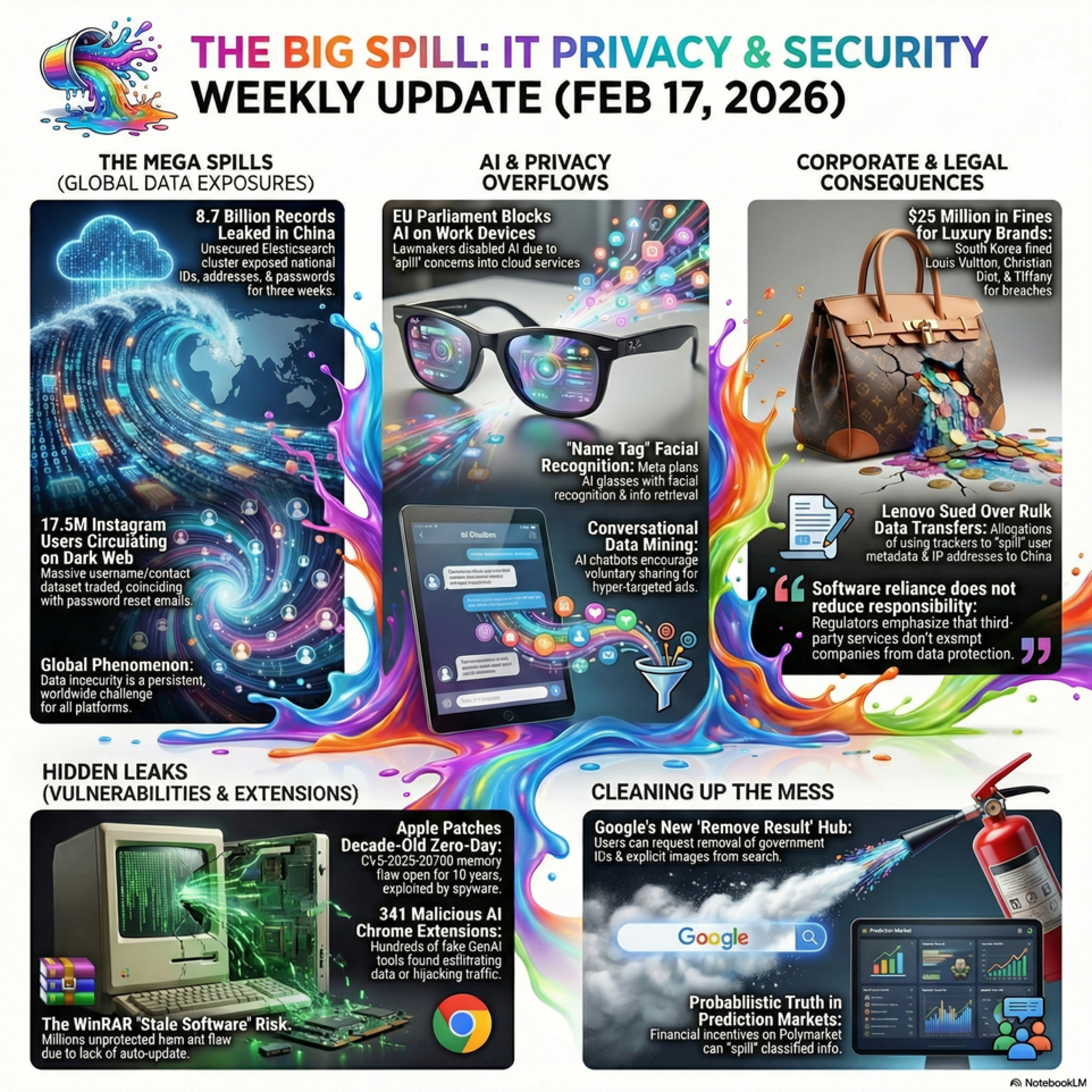 EP 279.5 Deep Dive. Spill, with the IT Privacy and Security Weekly Update for the week ending Feb 17th | We open with China’s 8.7 billion-record megaleak, framing misconfigured infrastructure as a planetary-scale risk rather than a local breach. Lenovo’s U.S. class action then shows how invisible web trackers can quietly “spill” American browsing data to China, while South Korea’s heavy fines against Louis Vuitton, Dior, and Tiffany illustrate that even luxury brands now pay real money when they mishandle customer information.The focus then narrows to individuals: a 17.5M-user Instagram dataset on underground forums, malicious GenAI Chrome extensions posing as helpers while siphoning data, and a decade-old Apple zero-day likely leveraged by commercial spyware all demonstrate how ordinary accounts and devices can become rich sources of exploitable data. Together they highlight a world where “just contact details,” browser add-ons, and long-lived bugs can escalate into serious compromise.From there, the update shifts into ambient surveillance and manipulation: Meta’s planned facial-recognition “Name Tag” for Ray-Ban smart glasses pushes identification into public spaces and raises new concerns about children and bystanders, while AI-saturated products from Google, Meta, and others quietly convert intimate conversations and searches into highly targeted ad fuel. It closes with a Shakespeare quote about guilt “spilling” itself and a sign-off urging listeners to “pour with a steady hand,” tying the spill metaphor back to handling data, tools, and trust more carefully in everyday digital life. | — | ||||||
| 2/18/26 |  Spill, with the IT Privacy and Security Weekly Update for the week ending Feb 17th., 2026 | EP279. This week's update spills on a global scale. We start with...A single misconfigured database just turned 8.7 billion Chinese records into a global reminder that at planetary scale, data protection failures stop being “incidents” and start looking like infrastructure risks.A new class action against Lenovo puts a spotlight on how invisible trackers and cross-border data flows can turn an ordinary website visit into a quiet export of American browsing habits to China.When Louis Vuitton, Dior, and Tiffany rack up multimillion-dollar privacy fines in South Korea, it sends a clear message: even the most glamorous brands pay dearly when customer data is treated carelessly.The Instagram dataset circulating on underground forums shows how a trove of “just usernames and contact details” can still supercharge scams, phishing, and harassment at massive scale.Dozens of AI-branded Chrome extensions masquerading as helpful assistants reveal how attackers now weaponize the GenAI buzz to sneak data exfiltration straight into your browser.Apple’s fix for a ten-year-old iOS and macOS zero-day pulls back the curtain on a long-running hole likely exploited by commercial spyware against some of the world’s most high-value targets.Metas planned facial recognition for Ray-Ban smart glasses pushes the privacy debate from your screen to the street, raising uncomfortable questions about who gets to be identified, by whom, and when.The rush to embed AI into every digital interaction is quietly reshaping advertising, turning your casual chats and searches into some of the richest targeting data the tech giants have ever seen.Grab a towel and let's check the spill. | — | ||||||
Showing 25 of 170
Sponsor Intelligence
Sign in to see which brands sponsor this podcast, their ad offers, and promo codes.
Chart Positions
6 placements across 6 markets.
Chart Positions
6 placements across 6 markets.
